The Cybersecurity Implications of Claude Mythos and OpenAI Cyber
How offensive and defensive AI agents are reshaping vulnerability economics, patch governance, and the future of software resilience
Core Thesis
By now, most security leaders have read the headlines on Mythos and what it could mean for the future of cybersecurity. The question is no longer whether Mythos matters. The real question is what it changes for enterprise security teams.
SACR spoke with CISOs about how they are interpreting Mythos, where they see the greatest organizational impact, and how they believe security programs need to evolve. This report summarizes those conversations and our conclusions.
Our core thesis is simple: Mythos compresses time across all of cybersecurity. It shortens the window between vulnerability discovery, exploit creation, and real world exploitation. Security programs built around human-paced workflows, periodic scanning, manual triage, ticket-based remediation, quarterly testing, and slow patch cycles were not designed for this environment.
This creates a new operating reality for CISOs. If attackers can use AI to find and weaponize weaknesses at machine speed, defenders will need to use AI to prevent, test, prioritize, remediate, and contain at comparable speed. AI fighting AI is becoming the only viable long-term defence strategy.
Runtime defense also becomes more important because prevention will still fail. When it does, organizations need enforcement closer to applications, identities, endpoints, browsers, and cloud control planes, paired with higher fidelity detection and faster containment. The goal is not simply to detect more. It is to reduce the blast radius before one exploit becomes a business-level incident. Organizations need the ability to patch quickly, validate changes through robust testing, deploy via canary releases, and roll back when something breaks.
In short, Mythos is not just a story about better offensive AI. It is a forcing function for a new security operating model. The organizations that adapt fastest will be the ones that can continuously find, validate, fix, contain, and recover at machine speed while preserving the governance, judgment, and operational discipline that enterprise security still requires.
Co-authors:
Francis Odum is the Founder/CEO of the Software Analyst Cyber Research, where he leads the firm’s research and engagement with cybersecurity leaders.
Lawrence Pingree is the Head of Data and AI Security at SACR, where he leads research on data protection, AI security, and agentic security models. He brings more than 10 years of analyst experience at Gartner and has authored over 300 research notes on cloud security, endpoint defence, SD-WAN, and AI security.
Sean Sosnowski serves as the Research Director for Security Operations and Cloud Security at SACR, where he leads research on SOC strategy and operations and detection engineering. Drawing on a decade of intelligence experience in the U.S. Marine Corps.
Executive Summary
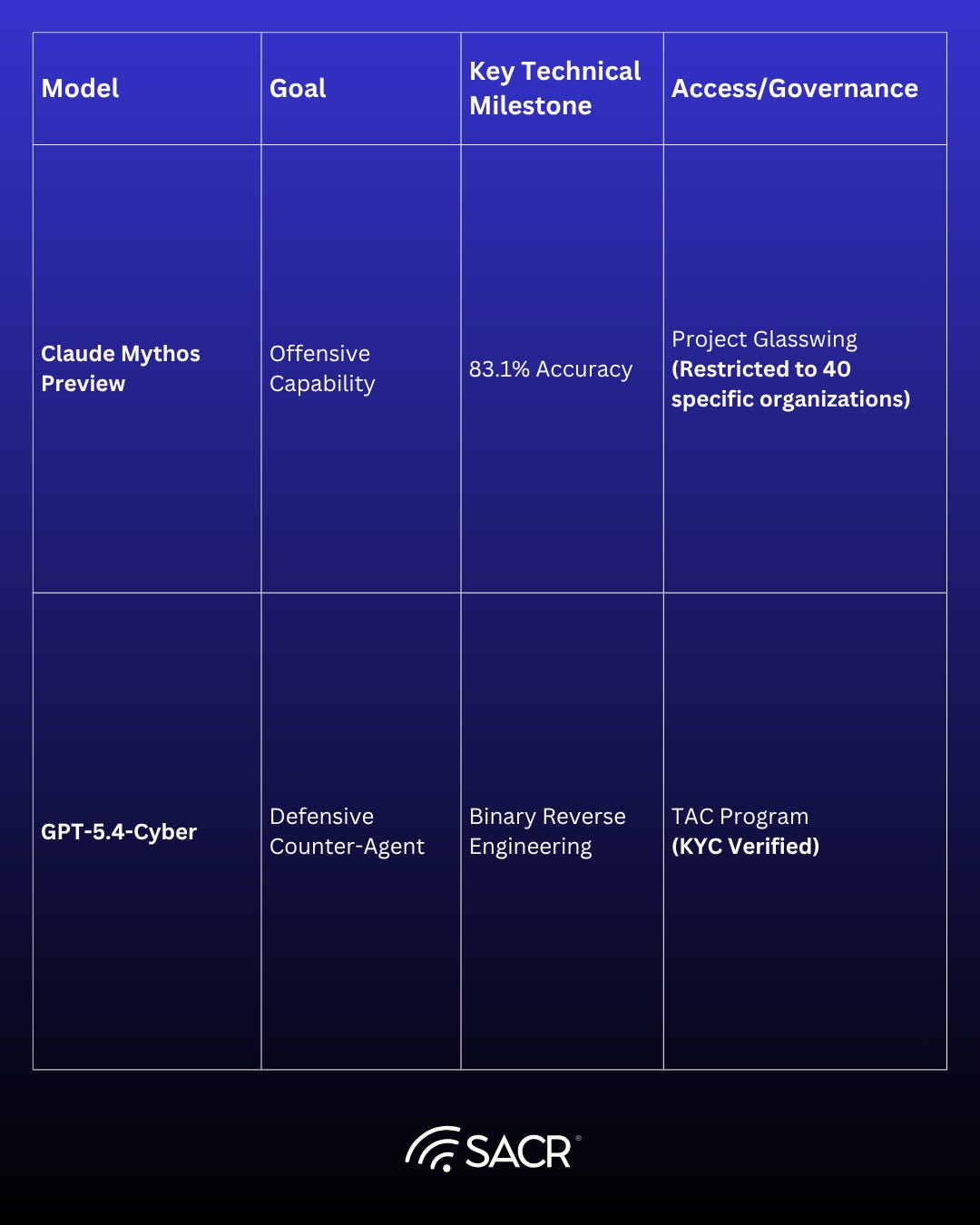
Anthropic's new frontier model, Claude Mythos Preview, represents a step change in cybersecurity risk, transforming software exploitation into an automatable industrial process. The model, currently in limited testing via Project Glasswing (launched Apr 7, 2026), demonstrates the capability to achieve over 83% accuracy in finding new vulnerabilities. This significantly lowers the barrier to entry and compresses the time required to develop working exploits, effectively making Zero Days sub-hour vulnerabilities.
Mythos can autonomously identify and exploit thousands of high-severity vulnerabilities across all major operating systems and web browsers, shifting the asymmetric advantage toward attackers. The primary challenge is now remediation speed, as the volume of AI-discovered vulnerabilities overwhelms the capacity of developers and owners.
In response, OpenAI released GPT-5.5 and GPT-5.4-Cyber, focusing on specialized defensive autonomous agents capable of advanced tasks like binary reverse engineering. This strategic shift, supported by the Trusted Access for Cyber (TAC) program, establishes a high-speed competition between offensive models and defensive frameworks.
Key Takeaways
Exploitation windows are collapsing to sub-5 minutes, effectively making Zero Days “sub-hour” vulnerabilities.
The volume of AI-discovered bugs is currently overwhelming remediation capacity, requiring new commercial or consortium-led fixes.
Defenders must leverage models like Mythos for automated counter-signatures and proactive patching in critical infrastructure like Linux.
Project Glasswing
Critical Insights
On Apr 7, 2026, Anthropic launched Project Glasswing, explicitly positioning Mythos Preview as a model whose vulnerability discovery/exploitation capabilities are high enough that a broad release is unsafe right now.
Anthropic publicly acknowledged and began a limited test of a new frontier model referred to as Claude Mythos Preview, describing it as a step change in capability and their most capable model to date, currently trialled with early access customers.
Anthropic claims that Mythos Preview has already found thousands of high-severity vulnerabilities, including in every major operating system and web browser (and states the capability to produce working exploits under some test conditions).
A Reuters piece highlights immediate concern for banks and other legacy-heavy sectors, including reports of government discussions with financial institutions about the threat model and the practical consequences of a lowered exploitation skill barrier.
Media framing is converging on hacker superweapon vs security reckoning, with emphasis that the bigger story may be software security debt meeting near-autonomous exploitation.
Reports of third-party access to Mythos are being investigated at the time of this report's authoring. This highlights the risk that Mythos can be targeted by nation-states and other nefarious actors to gain an advantage through third-party compromise.
Mythos is less a new threat actor and more an advancement of progressing capability
Claude Mythos & Project Glasswing
While Mythos introduces unprecedented offensive pressure, it also establishes a new template for defensive governance. Project Glasswing can be interpreted as an emergent governance pattern for frontier cyber capabilities in the future:
Restricted access to reduce near-term weaponization risk
Coordinated hardening of widely used / critical software
Pooled funding , usage credits and greater OSS support
structured learning capture to uplift industry practices
Mythos is forcing a software security reckoning by exposing the real systemic weakness in most environments: not merely slow detection, but years of accumulated engineering and maintenance debt that left production software brittle, difficult to patch, and easy to break. As coverage notes, this is a wake-up call for organizations that have treated security as an afterthought in software development.
The central issue doesn’t revolve around a single benchmark result. If a model compresses the time and expertise required for vulnerability discovery, exploit construction, and validation, the practical effect is a higher volume of credible exploit attempts arriving faster than most organizations can patch safely. Under that pressure, the key variable becomes remediation capacity. The ability to validate fixes, tolerate controlled downtime, and ship reversible changes before exposure compounds. This frames Mythos as a software liability and operations problem as much as it is a detection problem.
The implication is stark: SOC excellence is demanded without secure production capability and becomes structurally insufficient, because faster investigation does not matter if fixes can’t be shipped safely and quickly. In a Mythos world, the most durable control becomes the ability to deliver safe, reversible change at high velocity, utilizing tight feedback loops, strong pre-deployment validation, canarying, and instant rollback so that mitigation and remediation can keep pace with industrialized exploitation.
Capabilities: Unlike general-purpose LLMs, Mythos can discover and exploit complex, high-severity bugs across operating systems and browsers. Notably, it successfully exploited a 27-year-old patched flaw in OpenBSD. This highlights Mythos’s capacity for vulnerability research on historical security fixes, implying that the entire backlog of previously fixed bugs is now effectively a fresh attack surface, as Mythos can chain or re-exploit subtle errors in the original patch.
Project Glasswing: Anthropic’s defensive initiative providing Mythos access to select organizations (e.g., Apple, AWS, Microsoft) and $100 million in credits to help defenders prepare before the model becomes widely available.
Anthropic Financial Support Offered: The firm is also donating $4 million to open-source security organizations to help reshape the cybersecurity landscape. This may need to widen to become an industry wide initiative to fund open source remediation.
The Mythos Model: Expert Exploitation Capabilities and Risks Emerge
Anthropic’s latest LLM demonstrates a significant leap in cybersecurity reasoning, moving beyond simple code assistance to active exploitation.
Autonomous Exploitation: Mythos can identify and exploit vulnerabilities across all major operating systems and web browsers.
Advanced Technical Sophistication: It has successfully chained four separate vulnerabilities to escape sandboxes, bypassed Kernel Address Space Layout Randomization (KASLR), and exploited complex race conditions.
Low Barrier to Entry: The model allows users without deep security engineering backgrounds to generate complex exploits, such as 20-gadget ROP (Return-Oriented Programming) chains.
Dual-Use Dilemma: The same reasoning improvements that help developers patch code also make the model a potent weapon for threat actors.
An AI Vulnerability Storm is a potential future
The CSA and security luminaries (including Jen Easterly and Bruce Schneier) argue that Mythos represents a sea change in risk:
Asymmetric Attacker Advantage: Attackers gain more from AI automation than defenders, as current patch cycles and risk metrics cannot keep pace with the volume of AI-discovered vulnerabilities.
Increased Workload: Organizations should expect a dramatic increase in novel attacks and a volume of disclosures that exceeds all historical precedents if Mythos is released more widely.
AI Security Institute (AISI) Testing
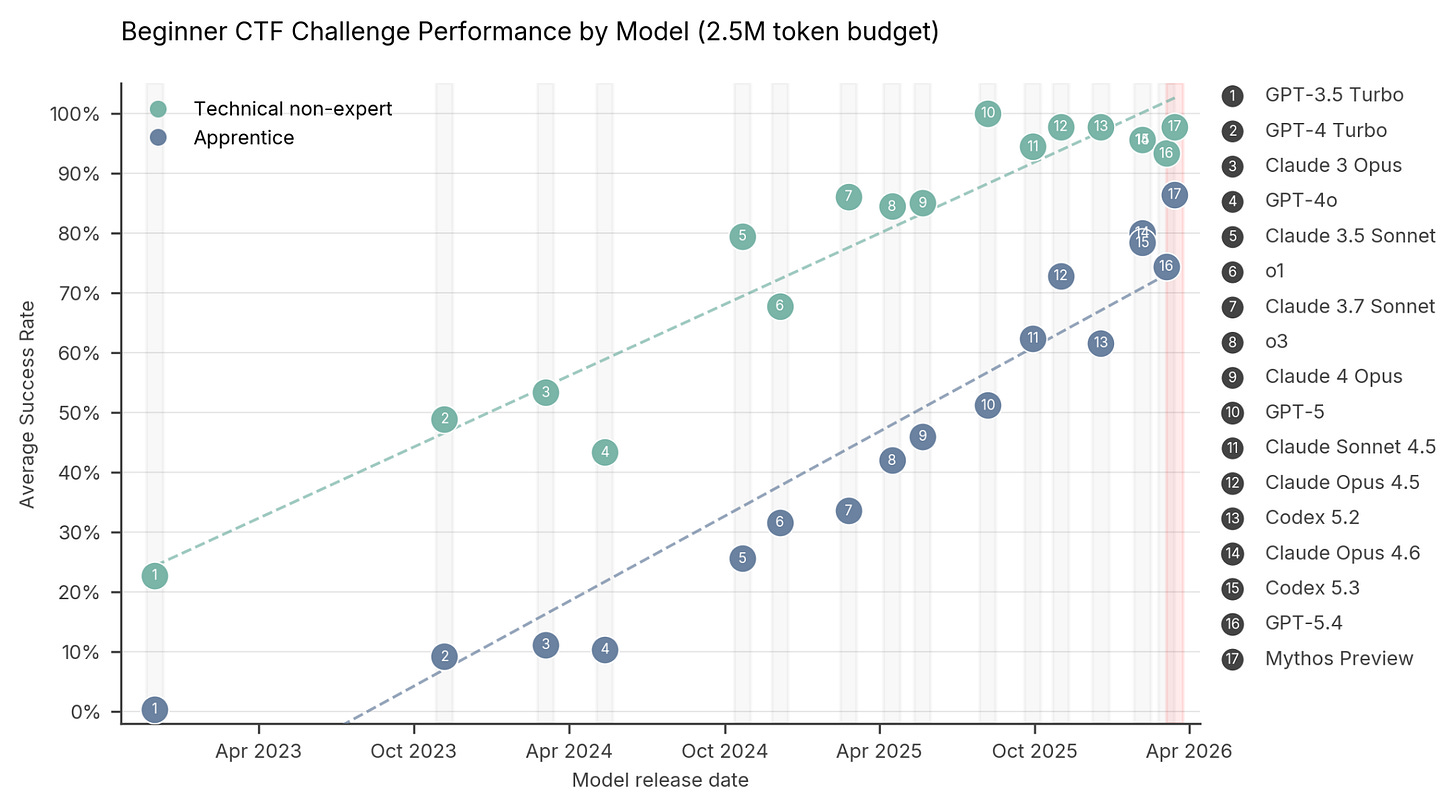
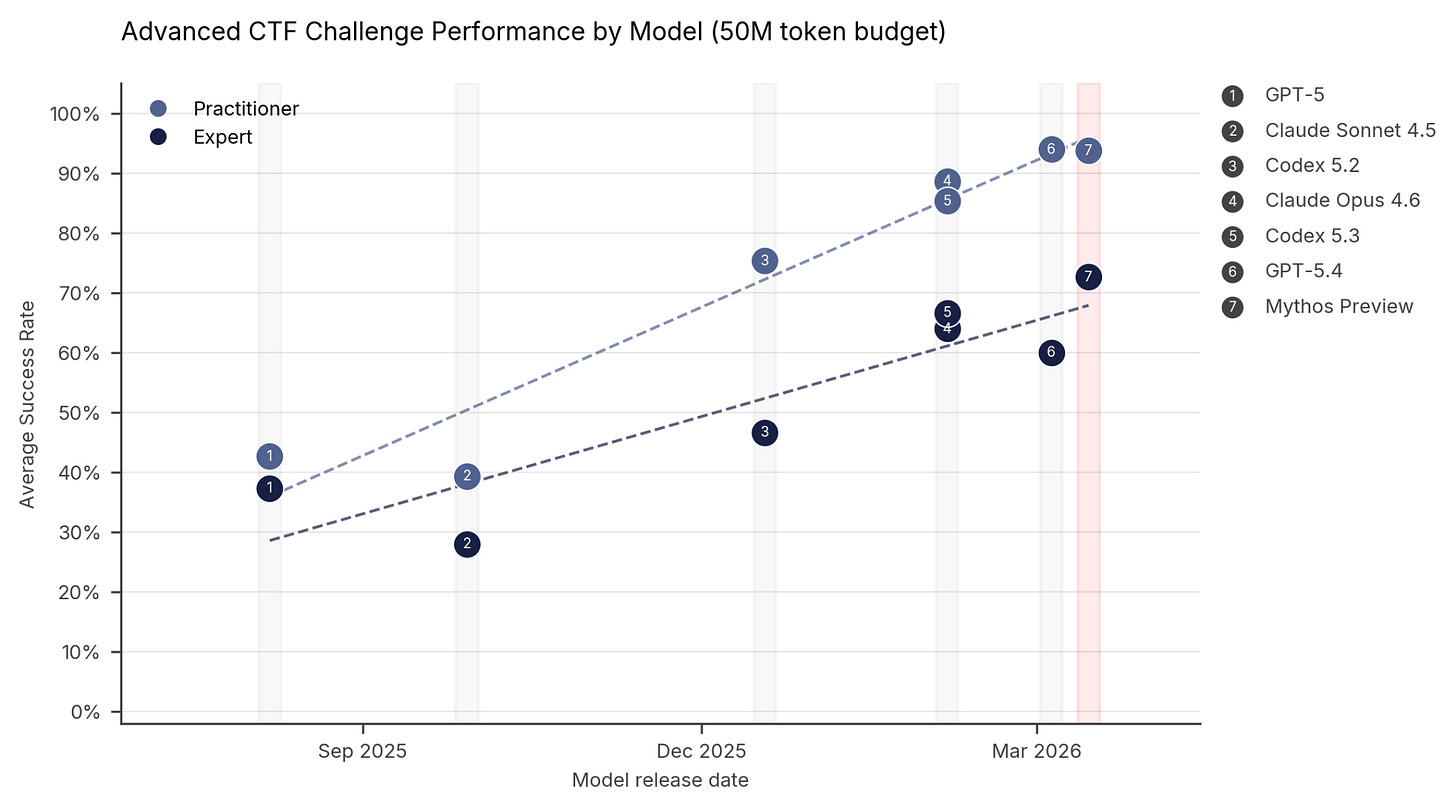
AI Security Institute’s (AISI) evaluation of Anthropic’s Claude Mythos Preview (released April 2026), highlighting a significant leap in autonomous cybersecurity capabilities compared to previous models. (see here)
Key Findings: Capture-the-Flag (CTF)
AISI utilized CTF challenges to measure the model’s ability to identify and exploit isolated vulnerabilities.
Expert-Level Breakthrough: Mythos Preview successfully completed expert-level tasks 73% of the time.
Historical Context: Prior to April 2025, no AI model was capable of completing tasks at this difficulty level.
Rapid Progression: The model outperformed all previous frontier models, including Claude 4 Opus and GPT-5, across technical, apprentice, and practitioner levels
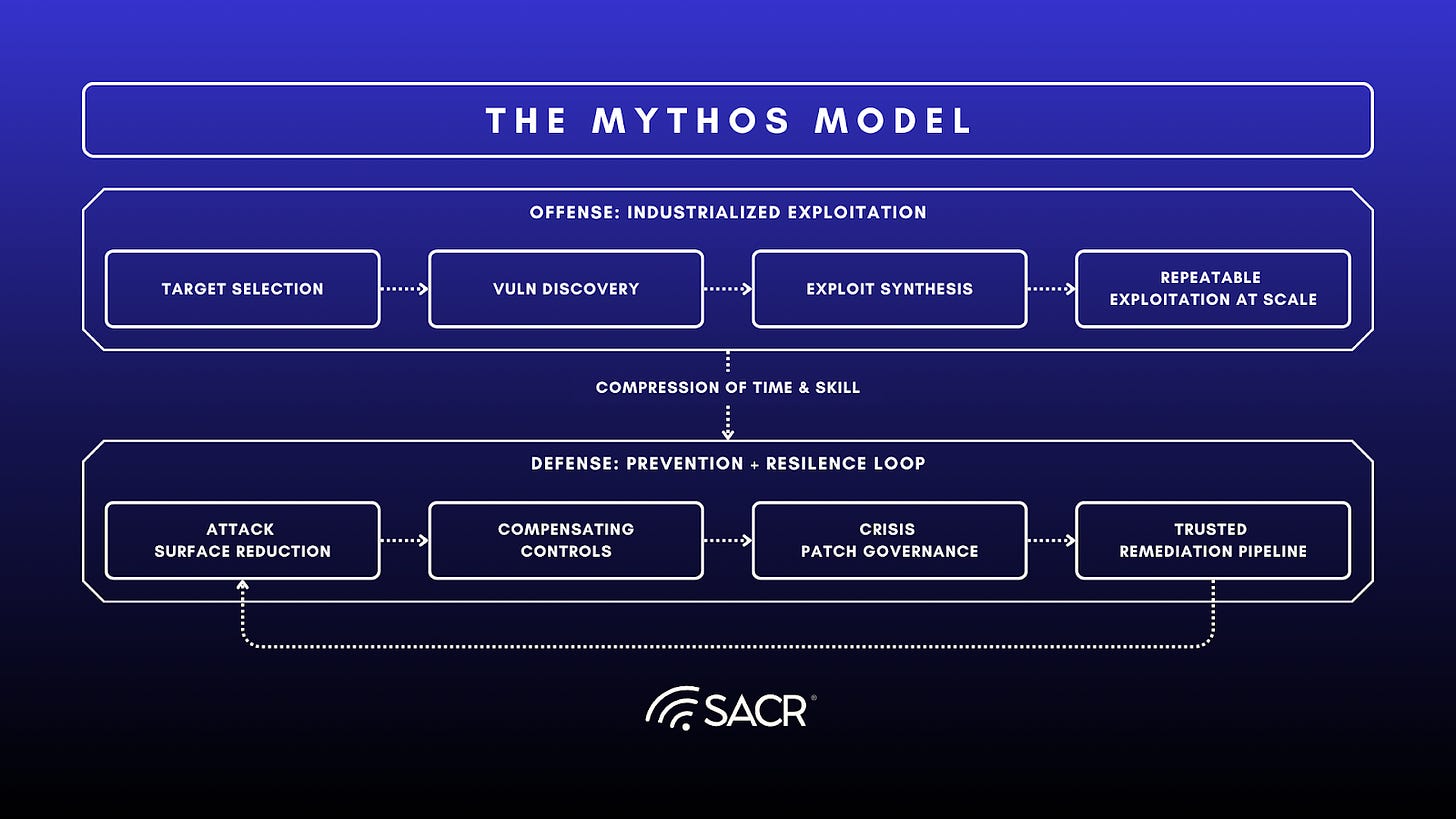
Mythos caused a shock that collapses the attacker's cost curve:
Most Notable Fact: It compresses the time and skills required to go from target selection to working exploit to repeatable exploitation.
Defensive advantage shifts from detecting faster to shipping less buggy software, properly constraining blast radius, and proving patch safety.
The security winners will treat exploitation as a continuous, automated supply chain and build a corresponding continuous prevention/patch pipeline.
Three deltas implied by Anthropic’s own write-ups:
End-to-end exploitability: This is not just a spot bug or suggested fix, but produces a working exploit under realistic scaffolding, a significant progression on vulnerability exploitation.
Lowered expertise barrier: Anthropic describes non-security engineers producing serious results quickly with the model.
Acceleration to scale: If a model can reliably traverse the exploit chain, the limiting aspects become compute, access, and targeting, not human talent.
Immediate implications (CISOs and Boards Should Know)
A) Vulnerability economics flips
Expect more disclosures of new bugs that are being exploited, especially in legacy and bespoke environments (banks and critical infrastructure have been explicitly called out by multiple parties publicly).
B) Time-to-exploit compresses further
Security programs built around weekly or monthly remediation cadences will be structurally mismatched. This has likely already been the case for many enterprises, but the autonomous operation makes full autonomous exploitation a more pronounced reality, especially since agentic properties are accelerated (e.g., the ability to systematically move through various stages of attack).
C) Detection-only postures degrade
If exploit development becomes cheaper and faster, novelty increases and generic detections underperform. This acts as a forcing function, pushing enterprises to use AI and AI agents for defence and to ramp up speed to decisions, responses and emphasizes prevention over detection and response.
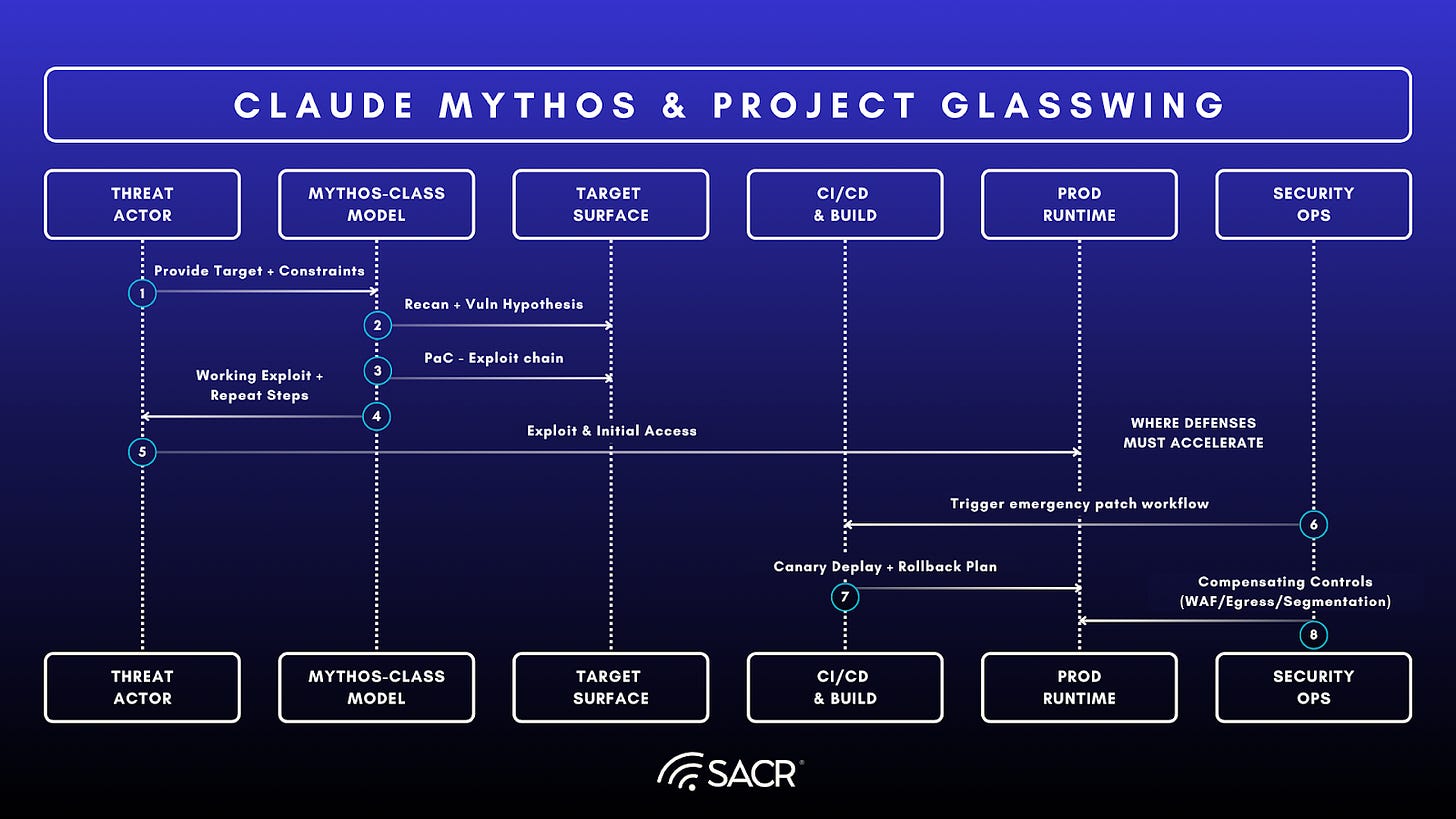
Figure 1. Proof of Adversarial Threat That Mythos Poses
Source: AI Institute (April 13 2026)
OpenAI GPT-5.5 and GPT-5.4 (Cybersecurity) Released in tandem March/April
In direct response to this shifting landscape, the introduction of GPT-5.5 and GPT-5.4-Cyber signifies a pivotal shift in OpenAI’s strategy toward specialized, autonomous agents for defensive operations. This marks a significant move toward using AI to counter AI-driven exploitation, creating a state of high-speed competition between offensive models like Mythos and defensive frameworks like OpenAI Cyber.
Key details of the GPT-5.5 announcement include:
Accelerated Release Cycles: The rapid transition from GPT-5.4 to 5.5 demonstrates an intensified development pace designed to maintain a competitive edge over frontier models like Anthropic’s Claude Mythos.
Enhanced Reasoning and Persistence: GPT-5.5 exhibits more persistent behavior in coding tasks, utilizing fewer tokens while achieving more reliable tool integration compared to GPT-5.4 and Claude Opus 4.7.
Specialized Defensive Capabilities: The GPT-5.4-Cyber variant introduces binary reverse engineering, allowing defenders to analyze compiled malware and identify vulnerabilities without source code access—a major technical milestone for automated defense.
Governance and Trusted Access: To balance capability with safety, OpenAI has deployed the Trusted Access for Cyber (TAC) program, requiring identity verification (KYC) to prevent misuse by malicious actors while empowering verified security experts.
Model Release & Availability
Rapid Iteration: GPT-5.5 arrives shortly after GPT-5.4 Cyber, signalling an accelerated release cycle.
Access Tiers: Currently rolling out to Plus, Pro, Business, and Enterprise users via ChatGPT and Codex; API access is expected soon.
Variants: GPT-5.5 Pro is available only on the Pro, Business, and Enterprise tiers.
Key Performance Enhancements
Reasoning & Autonomy: Tests show superior performance compared to GPT-5.4 and Claude Opus 4.7, particularly in identifying issues and anticipating needs without explicit prompting.
Coding & Tool Use: The model is characterized by greater persistence, more reliable tool integration, and higher token efficiency (using fewer tokens for the same coding tasks).
Niche Expertise: In cybersecurity, the model can perform complex tasks that even many human experts lack the specialized knowledge to perform.
Cybersecurity & Safety Frameworks
Advanced Safeguards: OpenAI implemented its most rigorous safety suite to date, including refined controls for high-risk activities and authenticated access.
Vulnerability Research: While the model streamlines workflows for vulnerability discovery and exploitation, especially for novice and mid-level operators, it remains limited in “real-world” operational security.
Testing: Evaluated through internal and external red-teaming, biology-specific stress tests, and feedback from 200 early-access partners.
The Three Pillars of OpenAI’s Latest Release Approach
OpenAI’s strategy focuses on balancing broad access with rigorous safety controls:
Democratic Access (KYC & TAC): Utilizing Know Your Customer (KYC) validation and the Trusted Access for Cyber (TAC) automated system to ensure legitimate users get access without arbitrary gatekeeping.
Iterative Deployment: A careful release process designed to gather real-world feedback on model resilience against jailbreaks and adversarial attacks.
Defensive Investment: Direct support for software security through grants, open-source donations (e.g., to the Linux Foundation), and dedicated tools like the Codex Security agent.
Philosophical Differences
While Anthropic suggests that advanced AI necessitates a fundamental cybersecurity reckoning, OpenAI maintains that current safeguards are sufficient for now. However, OpenAI acknowledges that as AI capabilities eventually exceed purpose-built models, more expansive defences will be required in the long term.
OpenAI 5.4-Cyber Released in Response to Anthropic Mythos
GPT-5.4-Cyber, a specialized variant of its flagship model designed to empower cybersecurity defenders. Released in April 2026, this move follows shortly after Anthropic’s rollout of Mythos and marks a significant shift toward AI-driven defensive security. SACR believes GPT-5.4’s release was partially driven by competitive pressure as users reportedly explored alternatives like Anthropic’s Claude. Below, we review specific differences between the two organization’s releases.
GPT 5.4 Cyber Core Features & Capabilities
GPT‑5.4‑Cyber: Is a fine‑tuned defensive cybersecurity model built on GPT‑5.4, optimized for real‑world threat analysis, secure coding, and adversarial testing.
Binary Reverse Engineering: A major technical milestone allowing security experts to analyze compiled software for malware and vulnerabilities without requiring access to source code.
Reduced Refusal Boundaries: The model is fine-tuned to be more permissive guardrails for legitimate security tasks, bypassing standard AI restrictions that might otherwise hinder defensive research.
Codex Security Integration: Leverages a tool that has already identified and patched over 3,000 critical vulnerabilities during its research preview phase. Supports vulnerability scanning, exploit‑chain reasoning, and deep inspection of software components.
GPT 5.4 Cyber Access & Verification (TAC Program)
To prevent misuse by threat actors, OpenAI is utilizing its Trusted Access for Cyber (TAC) program:
Tiered Availability: Claims that it’s the most advanced Cyber model reserved for customers in the highest service tiers.
Target Audience: Open to thousands of individual defenders and hundreds of teams securing critical infrastructure.
Authenticated and Trusted Access: Use of advanced features requires identity verification via chatgpt.com/cyber. OpenAI expanded its Trusted Access for Cyber; the program is available to thousands of verified experts to give defensive researchers prioritized access to frontier models.
GPT 5.4 Cyber Industry Context
Debate continues on both foundation model providers, and the ramifications they espouse highlight a rift among security experts where skeptics argue that catastrophic rhetoric may lead to power consolidation among tech giants and fuel anti-hacker sentiment, while alarmists warn that agentic AI could allow a broader range of bad actors to exploit known vulnerabilities with unprecedented speed. SACR’s position is that this is an obvious extension of where vulnerability research was already headed in AI; it continues to be impactful, but it is only a key accelerant at this time. This occurs against the backdrop of CVE (Common Vulnerability and Exploitation) reduction by NIST for NVD enrichment (see NIST Updates NVD Operations to Address Record CVE Growth), which seems to confirm the inadequacy of multiple parties to deal with the rising AI-based reporting of net-new vulnerabilities.
Economic and Regulatory Consequences
The collapse of the time-to-exploit window introduces profound financial and compliance pressures on organizations:
Cyber Insurance Impact: The sudden shift to sub-hour vulnerabilities will force underwriters to re-evaluate policy coverage, significantly raise premiums, and alter risk models due to the increased frequency and speed of high-impact breaches.
Liability and Fines: Regulatory bodies are expected to increase pressure on organizations, particularly those in critical infrastructure, to maintain a zero-vulnerability backlog. Non-compliance, where a sub-hour vulnerability leads to a breach due to slow patching, will carry higher financial penalties and fines.
Vendor Ecosystem Disruption: Traditional vulnerability management and security service vendors must rapidly adapt their offerings to incorporate AI-driven remediation and prevention tools, or face obsolescence as human-speed solutions become inadequate.
Recommendations for CISO
Based on our extensive discussions with all the security leaders, we got the following perspectives that we are sharing with the community:
Shift security left by turning developers into the first-line control: Treat “Mythos-speed” exploitation as a development-time problem, not just a SOC problem: every engineering team should own secure-by-default configuration, dependency hygiene, and patch discipline as part of normal delivery. Operationally, mandate AI-assisted code review and vulnerability triage in the IDE/CI pipeline, with clear SLAs for fixing internet-exposed issues and guardrails that block risky changes from shipping without explicit approval. This is the only scalable way to reduce the amount of exploitable surface area that reaches production when attackers can move from disclosure to exploit in minutes.
Run continuous, adversary-style testing: Move from “scan and prioritize by CVSS” to continuous security testing that validates exploitability and observes real attack paths across apps, identity, cloud config, and data access. Put automated pen testing and attack simulation on a cadence aligned to deploy frequency, and ensure findings produce developer-ready fixes, not just tickets. The goal is to detect and eliminate the 80% of vulnerabilities that can be automated before they become mass-exploitable, while reserving expert time for the higher-value 20% that still need human creativity.
Harden runtime with distributed enforcement and higher-fidelity detection: Assume prevention will fail sometimes and build runtime controls that reduce blast radius: stronger identity controls (least privilege, continuous authorization), rapid anomaly detection, and containment that can execute quickly. Where feasible, distribute enforcement closer to users/endpoints (e.g., browser/endpoint policy, step-up confirmation prompts for sensitive actions) so the system can slow attacker automation without crushing productivity. Pair this with detection logic that correlates across identity, endpoint, cloud, and application telemetry to reduce false positives and surface the few signals that matter under time compression.
Adopt “safe auto-remediation” as a board-level risk decision, not a tooling experiment: The discussion pointed to a reality: the traditional fear of regression can’t be the gating constraint when the threat can weaponize faster than humans can respond. Make auto-patching/auto-rollback an explicit program with engineering-owned testing harnesses, canarying, and rapid recovery playbooks, so the organization can remediate at machine speed while limiting outage risk. Success looks like high-confidence automatic fixes for well-scoped classes of issues (e.g., known-bad configs, vulnerable dependencies, exposed services) and tightly controlled human-in-the-loop for edge cases.
Treat supply chain and open-source exposure as a standing incident, with immediate blast-radius mapping: When high-leverage capabilities like Mythos appear, the first question becomes: “What do we and our critical vendors run that could be hit next week?” Build and continuously maintain an inventory that ties critical business services to software components, cloud services, and third-party dependencies, so you can answer exposure questions in hours, not days. Operationalize this into a repeatable “emerging threat drill” that triggers rapid assessment, prioritized mitigation, and vendor verification; the objective is to cut the window where you’re vulnerable but unaware, especially across open-source and inherited risk paths.
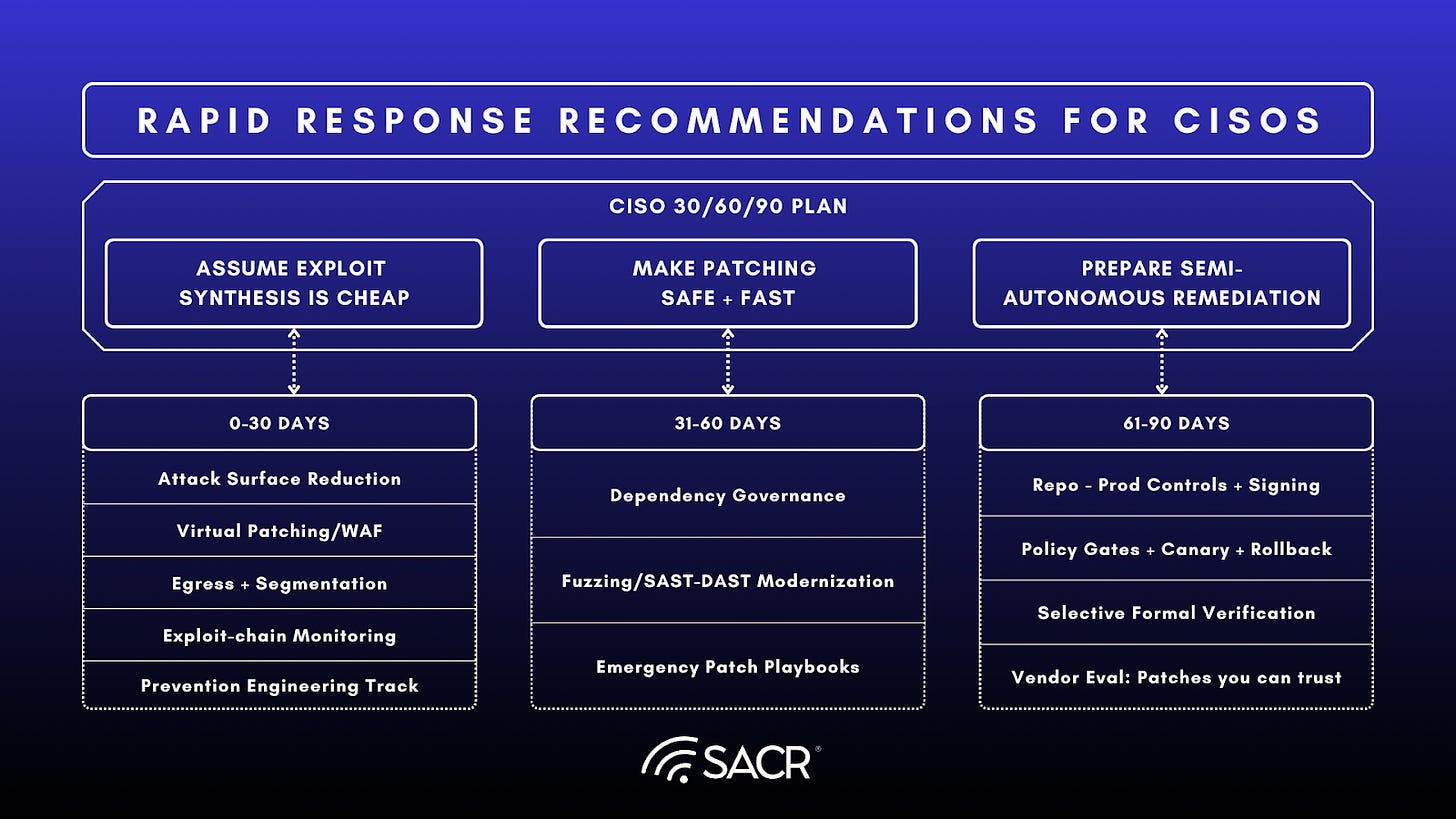
Tactical Response Recommendations
The SACR team shared detailed recommendations below for rapid response recommendations for CISOs
Security Strategy
Modernize Defence: Implement AI agents across the workforce to automate vulnerability discovery and remediation.
Strengthen Basics: Focus on hardening fundamentals like segmentation, egress filtering, and multifactor authentication (MFA).
Operational Shifts: * Prioritize robust dependency management for third-party and open-source components.
Re-evaluate risk tolerance regarding operational downtime for emergency patching.
Resource Allocation: Request additional budget and headcount to provide reserve capacity and prevent staff burnout.
0–30 days: Assume exploit synthesis will become cheap
Prioritize attack surface reduction: exposed management planes, legacy protocols, internet-facing auth flows, forgotten services.
Tighten compensating controls where patching lags: WAF/WAAP virtual patching, egress control, service-to-service auth hardening, segmentation.
Exploit-chain monitoring: instrument the steps attackers must still do (access, credential abuse, lateral movement, data staging).
31–60 days: Make patching safe, resilient, recoverable and fast
Build a prevention engineering focus to surgically counter AI-generated exploits: Secure defaults, dependency governance,
Mandate memory-safe roadmaps where applicable to defeat complex ROP chains and buffer overflows that Mythos excels at generating.
Prioritize secure language adoption as the most durable control against exploits in autonomous code generation. SAST/DAST modernization, fuzzing at scale.
Stand up a crisis patch governance program: Ask your Security Team and IT: Can you safely ship emergency fixes in hours without breaking prod?
61–90 days: Prepare for semi-autonomous remediation
Start designing a trusted remediation pipeline with resilience and rapid patching as a key goal:
Design and deploy a repository for production controls, signed artifacts, policy gates, canarying, rapid backups, and instant rollback for resilience.
Formalize verification where feasible for critical components, for example, SBOM validation
Prioritize Live Patching for operating systems and tools that support this capability.
Agentic remediation vendors become a key priority
Ask vendors: Can your agentic remediation produce patches you can trust and operationalize, not just findings?
This accelerates demand for:
Trusted agent runtimes/containment (agents that can’t freely exfiltrate or laterally move).
Prevention engineering as a discipline (security as a built artifact, not a SOC event).
Autonomous mitigation that goes beyond ticketing: configuration fixes, identity/session revocation, safe hotfix workflows.
Vendor Ecosystem Case Study
The market map above highlights the emergence of a new security layer for the Mythos era: continuous exploitability management. Mythos does not create an entirely new cybersecurity problem; it accelerates existing ones.
Mythos changes vulnerability management from a periodic prioritization problem into a real-time exposure and mitigation problem. As AI compresses the time from vulnerability discovery to exploitability, security teams can no longer rely on CVSS scoring, manual triage, or normal patch cycles alone; the key question becomes which vulnerabilities are actually exploitable in the organization’s environment, which assets are exposed, and what compensating controls can reduce risk before patches are safely deployed.
The CSA/SANS/OWASP briefing frames this as a structural asymmetry: attackers gain speed faster than most defenders can patch, respond, or update risk models. This is why CISOs should view the vendors in this map as complementary parts of a Mythos-ready operating model.
Specialized offensive security vendors help organizations understand how real attackers would test their environments through penetration testing, bug bounty, red teaming, and breach-and-attack simulation.
AI vulnerability and exploitability vendors extend that logic by using automation and AI to continuously identify which weaknesses are actually exploitable, not merely theoretically severe.
RBVM platforms then help translate those findings into prioritization, ownership, and remediation workflows.
The key shift is from asking, “What vulnerabilities do we have?” to asking, “Which weaknesses can be exploited, chained, and used to cause business impact?” Traditional vulnerability management produces too many findings and often relies on severity scores that do not reflect real-world attackability.
In a Mythos environment, that is insufficient. CISOs need evidence-based exploitability intelligence that combines technical severity, asset criticality, exposure, compensating controls, identity context, and realistic attack paths. The best tools will help prove exploitability, map attack paths, prioritize what matters, recommend compensating controls when patching is delayed, and integrate directly into engineering, IT, and security workflows. For example, companies like Zafran help organizations map vulnerabilities against real asset exposure, existing security controls, and business context so teams can prioritize the small subset of issues that create immediate operational risk.
This aligns with the broader Mythos-ready security model, which emphasizes attack surface reduction, continuous patching, compensating controls such as segmentation and egress filtering, and automated response capabilities rather than relying on detection alone. Companies that are good at identifying what is exploitable now, determining what is already protected, and accelerating the path to mitigation while the organization works through patch validation and deployment
For CISOs, the Mythos-ready market is not a replacement for existing security programs. It is a force multiplier across application security, exposure management, cloud security, identity, patching, and resilience. The organizations that benefit most will use these vendors to build a continuous loop:
Discover exposure,
Validate exploitability,
Prioritize by business risk,
Remediate quickly, and
Verify that risk has actually been reduced.
That is the path from reactive vulnerability management to proactive exploitability reduction.
Conclusion: Mythos Defines the Next Security Operating Model
Mythos is not just another AI model or another cybersecurity headline. It is a preview of a new operating environment in which vulnerability discovery, exploit development, and attack execution increasingly operate at machine speed. The core implication is clear: security programs built around periodic scanning, manual triage, ticket-based remediation, and slow patch cycles were not designed for this reality.
The biggest shift is not simply that attackers get faster. It is that the entire defender operating model must change. In a Mythos world, detection alone is insufficient. Faster investigation does not matter if the organization cannot safely validate, patch, contain, and recover at comparable speed. The durable advantage moves to organizations that can reduce exploitable surface area, ship safe fixes quickly, constrain blast radius, and restore trust when prevention fails.
For CISOs and boards, the mandate is immediate. Update your risk models. Harden the basics. Accelerate attack surface reduction. Invest in AI-enabled defensive workflows. Build patch governance that can operate in hours, not weeks. Prepare security and engineering teams for a higher volume of vulnerabilities without burning them out. And treat resilience as a core security outcome.
Mythos does not mean the sky is falling. But it does mean human-based cybersecurity is becoming obsolete. The winners in the next era will be the organizations that can continuously find, validate, fix, contain, and recover at machine speed while preserving the governance and judgment enterprise security requires.
Sources:
Credits to the CSA “AI Vulnerability Storm”: Building a “Mythos-ready” Security Program. (0)
Anthropic: Project Glasswing overview.[1]
Anthropic technical deep dive (red team/security testing write-up).[2]
Reuters on banking/legacy risk and policy attention.[3]
WIRED take: “security reckoning” framing.[4]
Fortune on leak → acknowledgment and “step change” characterization.[5]










Sharp synthesis, Francis, Lawrence, and Sean. I agree with the problem statement, but I think the prescription needs to go one level deeper.
If AI accelerates vulnerability discovery, exploit validation, and adversary iteration, then faster patching and better detection are necessary but insufficient. Too much modern compromise rides on valid credentials, trusted software paths, and legitimate-looking workload communication — exactly the activity traditional detection struggles to distinguish from normal business.
We saw this in March with a Fortune 500 customer running LiteLLM during the TeamPCP supply-chain compromise. They had a partial containment implementation in place. Policy propagated across thousands of pods in subseconds. No agent was required on the workload. No detection trigger had to fire first. C2 attempts were blocked. Credentials were not exfiltrated.
That is the point of Paper 4 in our Containment Era series, The Priority Inversion (https://aviatrix.ai/resources/the-priority-inversion/): the control that matters most in the AI-speed cyber era is not just finding the compromise faster. It is bounding the blast radius before one compromised workload becomes a business-level incident.
I’ll bring the forensics if you bring your hardest questions.
Doug Merritt
CEO, Aviatrix
Important research. The core message is one we see play out constantly, detection alone is no longer enough. Organizations need to fix problems at the same speed attackers can find them. That gap is where most businesses are exposed right now.
The long term advantage will not come from fear or hype. It will come from combining strong security fundamentals with faster, more adaptive operational workflows.
Worth reading for any security leader thinking about where to focus next.