Agentic Browsers and the New Last Mile in Cybersecurity: An Enterprise Guide to Browser Security In 2025
A practical maturity model for navigating the rise of agentic browsers, and how AI-powered interfaces are reshaping the attack surface for both enterprises and consumers.
Introduction: The Rise of Agentic Browsers
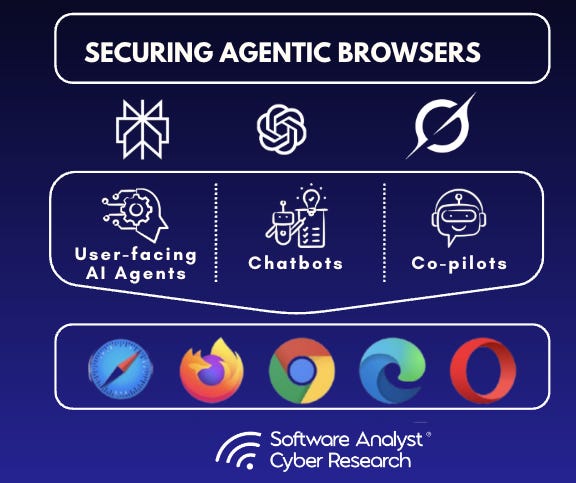
The web browser is undergoing its most profound change since its invention. With the recent moves from OpenAI, Google, and Perplexity, the browser is becoming a key attack surface as it evolves to become an agentic platform. It’s increasingly becoming an environment where users express intent in natural language, and AI agents execute tasks on humans’ behalf. Instead of manual clicks, agentic browsers integrate LLMs, APIs, and memory to summarize, synthesize, search, fill forms, and act autonomously across multiple sites. Increasingly, agents are going to be the dominant users of the internet through the browser, and this will represent a fundamental change in how trust, data, and control will be distributed on the internet.
This landscape is already taking shape:
OpenAI’s Operator aims to turn Chromium into an AI-first research/task engine. We know they are working on Opera’s Neon which experiments with local AI agents for creative tasks.
Google’s DeepMind Mariner plans to weave Gemini into Chrome with multi-tab orchestration and contextual editing;
Perplexity’s Comet is already the most active agentic browser, which eliminates search in favour of direct agent-driven results, and startups like Dia, Fellou, and Nanobrowser are pushing toward memory-driven and automation-heavy experiences. Collectively, these moves signal the browser’s evolution into the primary operating layer of the AI economy.
The timing is not coincidental. In 2025, every major AI player is racing to own the browser because of its unique strategic value. The browser is the most-used enterprise application, and therefore the gateway to user behavior, workflows, and data. It makes sense because of the data gravity. Browsers generate a constant stream of rich interaction data that can train and refine models. Owning the browser secures first-party access to this data.
We predict that by early 2026, agentic browsers will become the dominant use for most consumers. With agentic browsers, user attention shifts away from traditional apps and into prompt-driven workflows, redefining the very concept of an operating system. Whoever controls the browser controls the user’s digital environment, their data, and increasingly their workflows. This makes the browser both the most valuable interface and the most dangerous blind spot.
***
The Security Imperative in the Agentic Era
Just as traditional browsers became the last mile blind spot in enterprise security, agentic browsers risk becoming the new weakest link in AI-era digital infrastructure. They mimic human users without human judgment, and if left ungoverned, they could automate mistakes and exfiltrate sensitive data at machine speed.
The same capabilities that make agentic browsers powerful also open entirely new attack surfaces that are adjacent to AI security risks we’ve discussed in the past, for example, in this report on securing AI/LLMs. The risks compared to humans is that AI agents can be deceived, coerced, or hijacked through mechanisms invisible to traditional defences. For example; Prompt injection and UI traps, where maliciously crafted instructions or hidden elements redirect agents to harmful actions. There are cross-domain and plugin attacks, where third-party APIs or extensions exploited by agents create supply-chain vulnerabilities. There are other issues around memory misuse and data leakage that occur when agents retain and reuse sensitive information across sessions.
If enterprises can harden agentic browsers with visibility, control, and integrated safeguards, they can unlock the promise of AI benefits without exposing themselves to compromise. I partnered with LayerX Security, an enterprise browser extension security company, to explore why the browser is becoming central and how the browser is becoming the last mile for security. The goal of this report is to educate technology practitioners and cyber practitioners on an emerging risk area.
The report below sets a framework and implementation guideline for any security leader or practitioner wanting to secure enterprise browsers across their companies. Today, Perplexity, Opera or Gemini browsers aren’t fully established, so the report focuses on today’s enterprise browsers and speaks to the limitations of existing security controls for them. See the full report below. (You can also download a version here.)
The Browser As The New Frontier in Enterprise Security
In the past few years, the web browser has transformed into the primary workspace for employees. With hybrid work and cloud adoption, over 85% of the workday now takes place in a browser using SaaS and web apps. Employees access corporate emails, customer data, and critical applications all through a browser tab, often outside the corporate network on home or mobile devices.
In fact, 90% of organizations allow employees to access corporate data from personal (BYOD) devices, extending work beyond managed endpoints. Enterprises must treat agentic browsers as first-class actors in the threat model. Security needs to be embedded at the browser and agent layer itself.
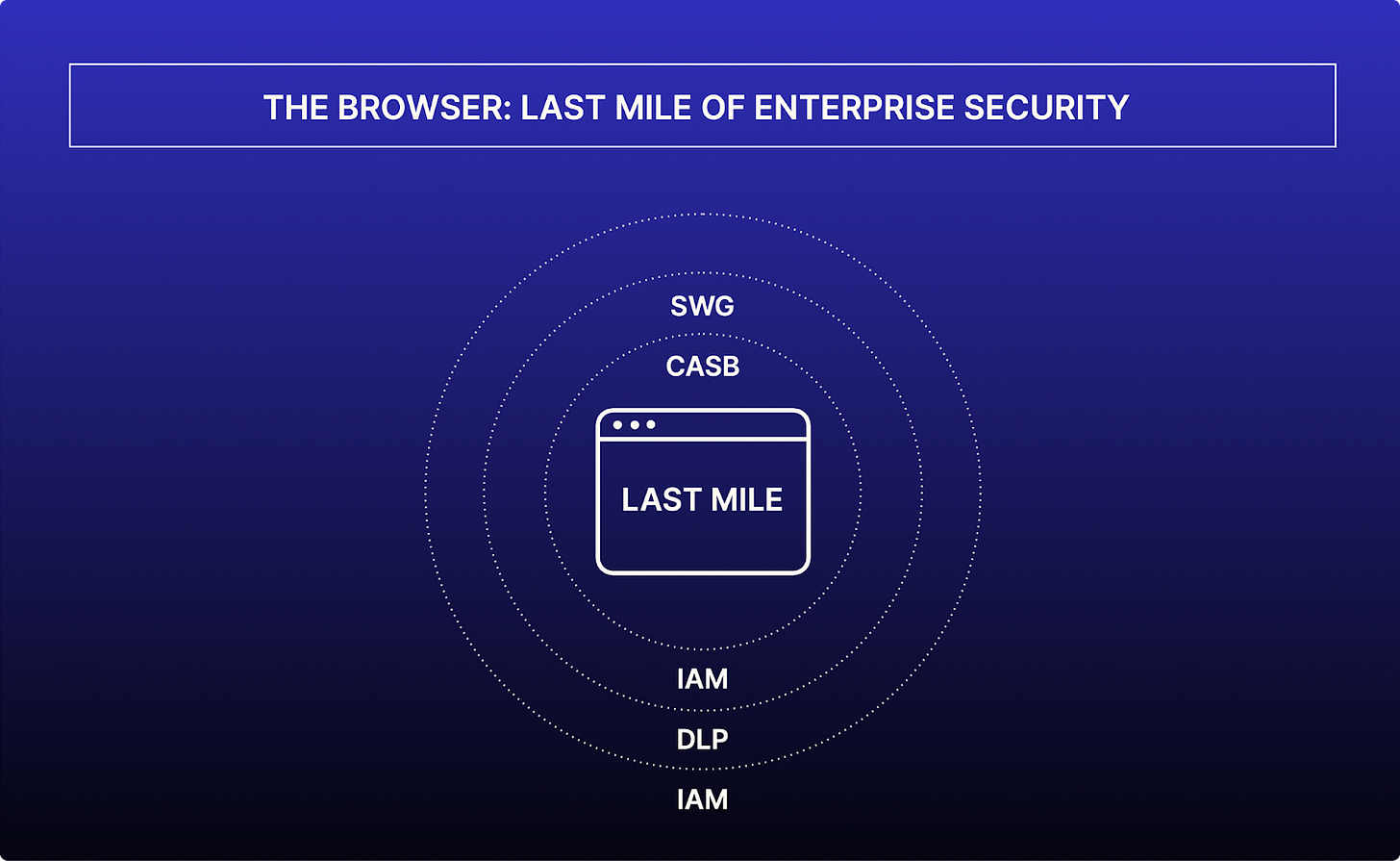
This shift has unlocked tremendous productivity and flexibility, but it has also expanded the attack surface to an unprecedented degree. The browser has effectively become the “last mile” of enterprise IT, the final interface between users and the internet, and adversaries have taken note.
Despite massive investments in security tools (from next-gen firewalls to Zero Trust cloud gateways), browsers remain a glaring blind spot in the security stack. Traditional defenses like Secure Web Gateways (SWGs), Cloud Access Security Brokers (CASBs), Endpoint Detection & Response (EDR), and Data Loss Prevention (DLP) platforms each cover part of the risk, yet gaps persist in that final stretch where users interact with web content. Attackers are actively exploiting this blind spot: 95% of organizations report experiencing a browser-based cyber attack, showing that nearly every company has had threats slip through the cracks via the browser. Whether it’s a drive-by malware download, a rogue browser extension, or sensitive data being unintentionally shared through a web app, these incidents underscore an uncomfortable truth, “the browser is now the biggest unsecured door into the enterprise”
Real-world Scenario
In 2024, a financial firm’s CISO was alarmed to discover that an employee had unknowingly installed a malicious Chrome extension on their personal laptop. The extension quietly siphoned corporate data and authentication cookies for months before detection. The existing security stack (CASB and endpoint AV) never noticed, because the data exfiltration happened entirely within the browser’s domain, a classic last-mile blind spot. Only after a major client’s data was found on the dark web did the company trace the breach back to the innocuous-looking add-on. Stories like this are increasingly common across industries.
Security leaders are beginning to ask hard questions: How do we safeguard corporate data across the new frontier of file-less data and SaaS applications, without hindering productivity? How do we extend Zero Trust principles to an environment where users seamlessly jump between work and personal web apps?
The answer requires reframing our approach. This guide tackles that challenge head-on, reframing the browser as both a critical risk area and an opportunity. By treating browser security as a first-class priority, organizations can close the gap in their Secure Service Edge (SSE), SWG, CASB, EDR, and DLP strategies. We will explore a practical maturity model for browser security and a roadmap that security executives can follow to systematically illuminate, control, and integrate the browser into their broader defense-in-depth strategy.
GenAI as a Catalyst for Enterprise Browser Security
Another key factor driving the adoption of browser-based security guardrails is GenAI adoption. The race for enterprises to use AI as a competitive advantage has accelerated in 2025 compared to the period of 2020. For the companies aiming to leverage gen-AI, they are struggling with a paradox: the same browser tab that empowers employees to brainstorm, code, and draft has also become the shortest route for sensitive data to escape corporate control.
Unlike earlier SaaS or mobile software trends, LLM interfaces invite users to paste raw source code, customer records, or strategic roadmaps directly into a third-party algorithm whose training corpus is opaque and whose retention policies are mutable. Every prompt is, in effect, an unsanctioned API call and traditional perimeter tools have no insight into where that payload lands once it traverses TLS and renders inside the DOM. That is why secure-by-design enterprise browser controls that have granular copy-paste DLP, prompt inspection, extension vetting, identity-aware session isolation, and real-time risk scoring have become the pole-position control point for AI-era governance.
Control Imperative
Enterprise browsers and security-grade browser extensions are uniquely positioned to close this gap. Deployed inline, they can:
Fingerprint and classify data before transmission.
Apply granular, identity-aware policies to clipboard, upload, download and prompt fields;
Redact or tokenize high-value attributes in real time; and
Stream enriched telemetry to SIEM, XDR and data-classification engines.
Based on the research of the Software Analyst, we are seeing boards already pressing CISOs for proof that confidential information fed into AI systems cannot resurface in public training sets, subpoenas, or insider theft campaigns; browser-native controls supply both the guardrails and the audit trail that answer the question.
Since solutions like DLP, SWG, CASB and EDR haven’t proven to capture this risk, enterprises are looking to browser security. We believe that by elevating the browser from passive rendering engine to active Zero-Trust sentinel, security teams reclaim the last mile without fracturing user experience, preserving innovation while extinguishing the riskiest exfiltration path. GenAI may compress the distance between creativity and compromise, but a hardened enterprise browser lengthens it, keeping the business ahead of the breach for years to come and resiliently.
The Blind Spot in Today’s Security Stack
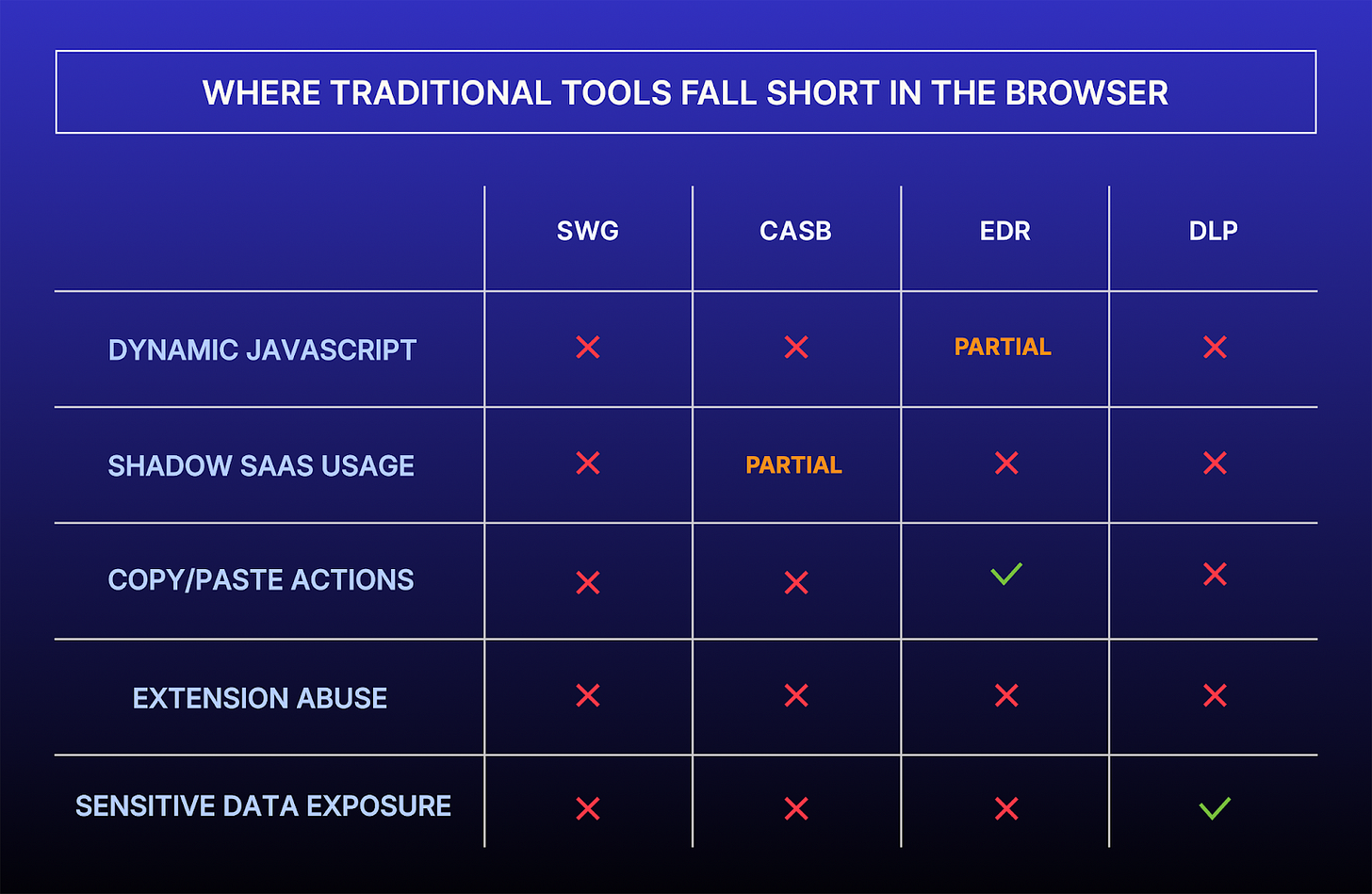
Modern enterprises have built layered defenses over the years: firewalls and SWGs to filter web traffic, CASBs to govern cloud app usage, EDR on endpoints to catch malware, DLP to prevent data leakage, and identity controls to verify users. Yet the browser itself where these controls converge, has remained largely ungoverned territory. Traditional tools struggle to fully protect what happens within the browser once a connection is allowed. Consider a few examples of where conventional security approaches fall short:
Data Loss Prevention: Traditional DLP solutions often rely on agents on managed devices or network proxies to scan for sensitive data in motion. They struggle with the granular context of browser actions, such as text a user copy-pastes from a secure CRM into an unsanctioned chat or the content of any file uploaded via a web form. Unless the DLP agent is tightly integrated with the browser, it may miss these last-mile data transfers. As one security architect lamented, “Our DLP can tell if someone emails out a client list, but it can’t stop them from copy-pasting that same list into a website like ChatGPT.”
Secure Web Gateway / Network Filters: SWGs can block known malicious URLs or content patterns, but they can’t always see dynamic, encrypted browser actions. Many attacks originate from legitimate websites compromised with malicious scripts or from new, unknown URLs. Modern web apps heavily use HTTPS and dynamic content, limiting what network-based tools can inspect. The result: a cleverly obfuscated script on a seemingly benign site can slip past network defenses and execute in the user’s browser. If that script isn’t outright malware caught by antivirus, it may go unnoticed while it quietly exfiltrates data.
CASB and Cloud Security: CASBs are designed to monitor and control access to sanctioned SaaS apps and to spot shadow IT usage by analyzing traffic. However, CASBs often rely on logs from managed devices or gateways. In a BYOD scenario or a direct-to-cloud connection, shadow SaaS usage can go completely undetected. An employee signing up for an unsanctioned online tool or uploading data to a personal cloud drive from their browser might evade CASB visibility until after the fact. CASB policies also may not intercept everything happening inside a legitimate app’s web interface (e.g. a user exporting data from Salesforce and uploading it to an unsanctioned service).
Endpoint Security (EDR/AV): Endpoint solutions focus on processes running on the device and known malicious binaries. But if an attack remains confined to the browser (e.g. injecting a malicious script into a page, or a user performing risky actions in a web app), it may not trigger traditional endpoint alerts. EDR might not register an incident where a user manually downloads sensitive files from a company app and then posts them to a public forum, because to the endpoint, that looks like normal browser and user activity. The browser’s own processes (like rendering engines and script engines) are often a black box to EDR unless the malicious code tries to break out of the browser sandbox.
In summary, existing security solutions leave a distinct gap between the network and the endpoint and the browser lives in that gap. The situation is worsened by the fact that standard browsers (Chrome, Firefox, Edge, etc.) were not built with enterprise security in mind. They prioritize user experience and compatibility, which is great for productivity but means out-of-the-box browsers lack the enterprise-class controls needed to protect sensitive data. This gap has turned the browser into a massive, vulnerable attack surface that attackers are exploiting with alarming frequency.
Evolving Risks: Why Browsers Have Become the Battleground
Today’s browser-centric threats
The risk landscape around browsers is rapidly evolving. It’s not just traditional malware and phishing anymore but a host of new challenges have emerged as work moves to the web. Below are some of the most pressing browser-related threats that mid-to-large enterprises face today:
GenAI Data Leakage: The rise of generative AI (ChatGPT, Bard, etc.) introduces a novel challenge: users willingly sharing sensitive data with external AI platforms in exchange for assistance. Consider the high-profile example of Samsung in 2023; engineers pasted proprietary source code into ChatGPT, only to realize later that the data had been inadvertently leaked outside the company. That incident led Samsung and others (like banks on Wall Street) to temporarily ban AI chatbot use. The dilemma is clear: these AI tools are incredibly useful, yet if used recklessly via the browser, they can become an automatic data exfiltration channel. A majority of organizations know this is a concern, over 65% admit they currently have no control over what data employees copy into AI tools. This lack of control is frightening in industries like finance or healthcare, where one paste of client PII into a chatbot could violate privacy laws. Attackers might not even need to phish data; users will unknowingly hand it to an AI. Thus, managing how corporate data is shared with online AI services has become a new facet of browser security.
Web/SaaS DLP: As work moves to cloud-based apps, sensitive information flows through countless web and SaaS channels like Slack, Google Drive, Dropbox, WeTransfer, LinkedIn, and more, that traditional DLP tools struggle to police. Users can leak data intentionally or accidentally on these platforms, often beyond the reach of legacy controls. Unlike classic file-based exfiltration (sending email attachments or uploading files), much of this leakage is "file-less", copying and pasting content, typing sensitive details into web forms, or sharing text snippets in SaaS chats. These in-browser actions typically don’t trigger the file-centric rules of older DLP systems. Most traditional DLP solutions were built to scan files and emails, not to inspect dynamic browser activity, as one analysis put it, “inline DLP was never built to control how employees handle data inside SaaS applications”. This leaves a blind spot: an employee could paste confidential data into a chatbot or personal cloud app without any red flags. Real-world scenarios underscore this gap: a developer copying API keys into ChatGPT or a salesperson exporting a client list to a personal cloud drive will quietly bypass corporate DLP alerts. The compliance implications are serious. Uncontrolled movement of regulated data into unsanctioned apps can violate laws like HIPAA or GDPR – for example, uploading an EU customer list to a U.S.-based SaaS or pasting patient records into an unsanctioned tool. In short, the browser has become a major data exfiltration channel, and without new web-focused controls, organizations risk sensitive data slipping away undetected.
Shadow SaaS and “Shadow AI” Applications: The average large organization uses around 10,000 different SaaS and web applications, far beyond the list of officially sanctioned apps. Employees, often with good intentions, sign up for new tools or try out AI-powered web services without IT’s knowledge. This “shadow IT” means corporate data can end up in unsanctioned apps or AI platforms with zero visibility or oversight from security. Every new web app or AI tool a user accesses via the browser could become a repository of sensitive data or a conduit for attack. For example, a marketing employee might use a free online graphic design tool to create a presentation, unknowingly uploading confidential product roadmaps to an external service. If that service is compromised or doesn’t enforce strong security, the data is at risk. Shadow AI tools (like unsanctioned generative AI SaaS) amplify the issue – users might feed proprietary data to an AI service to get some result, not realizing the service could learn from or even expose that data. Without browser-level monitoring, such usage is a blind spot.
BYOD and Off-Network Access: When users work from personal laptops or phones, IT loses a degree of control. Company data is accessed through browsers on devices where corporate EDR or DLP might not be installed. The result is that security policies can be easily bypassed, intentionally or accidentally. A recent industry study found 98% of organizations have experienced some form of BYOD policy violation by employees, underscoring how common it is for users to step outside official channels. This could be as simple as an employee downloading an official report via their home computer’s browser because it’s convenient. That home computer might be unpatched, running an old browser version, or even already infected with malware. Attackers often target personal devices knowing they are easier to breach, then use them as a pivot to corporate cloud apps via the browser. The challenge for security teams is enabling BYOD productivity without creating a gaping hole in defenses.
Unmanaged Browser Extensions: Browser extensions and add-ons can greatly enhance user productivity, from password managers to workflow tools, but they also pose a significant risk if not controlled. An extension runs with extensive privileges in the browser environment. A malicious or compromised extension can log keystrokes, read data on any website, or siphon session cookies. Unfortunately, most organizations do not closely monitor what extensions employees install. This has led to incidents where popular extensions with millions of users were hijacked or discovered to be secretly exfiltrating data. For instance, in late 2024 researchers uncovered 33 malicious Chrome extensions that had harvested data from over 2.6 million users over 18 months. In one case, an extension even stole authentication tokens for services like Facebook and ChatGPT. Such incidents highlight the supply-chain risk of extensions – even ones downloaded from official web stores can turn rogue via hidden updates. If an organization isn’t actively vetting or limiting extensions, it could be one install away from a major breach. This risk is especially acute in regulated industries, where an undetected data leak by an extension could violate compliance mandates without anyone realizing it for months.
Sophisticated Phishing and Web-Based Malware: While not new, phishing remains one of the most effective attack vectors, and it primarily plays out in the browser. Today’s phishing sites are highly sophisticated, often hosted on legitimate cloud platforms or using valid certificates, making them harder to detect. Users might be fooled into entering credentials on a fake login page or granting OAuth permissions to a malicious app, all via the browser. Likewise, malware delivery has evolved. Rather than rely solely on email attachments, attackers lure users to click links that open weaponized web pages. These pages can execute drive-by downloads or exploit unpatched browser vulnerabilities to install malware. Modern browsers update frequently to patch such holes, but if a user’s browser is not up to date (common on unmanaged devices), a zero-day exploit can silently compromise their system just by visiting a page. Notably, Google Chrome faced multiple zero-day attacks in 2023-2024, underscoring that even the latest browsers can have critical flaws. In regulated sectors, a single successful phishing or malware incident via the browser can trigger severe reporting requirements and reputational damage. The browser is essentially the frontline for these social engineering and exploit attacks.
The browser has become the battleground for a spectrum of threats from stealthy data leakage to active exploitation. Security leaders must widen their focus to include this user-facing layer. The following sections introduce a maturity model that organizations can use to methodically strengthen their browser security posture, addressing these risks through improved visibility, control, and integration.
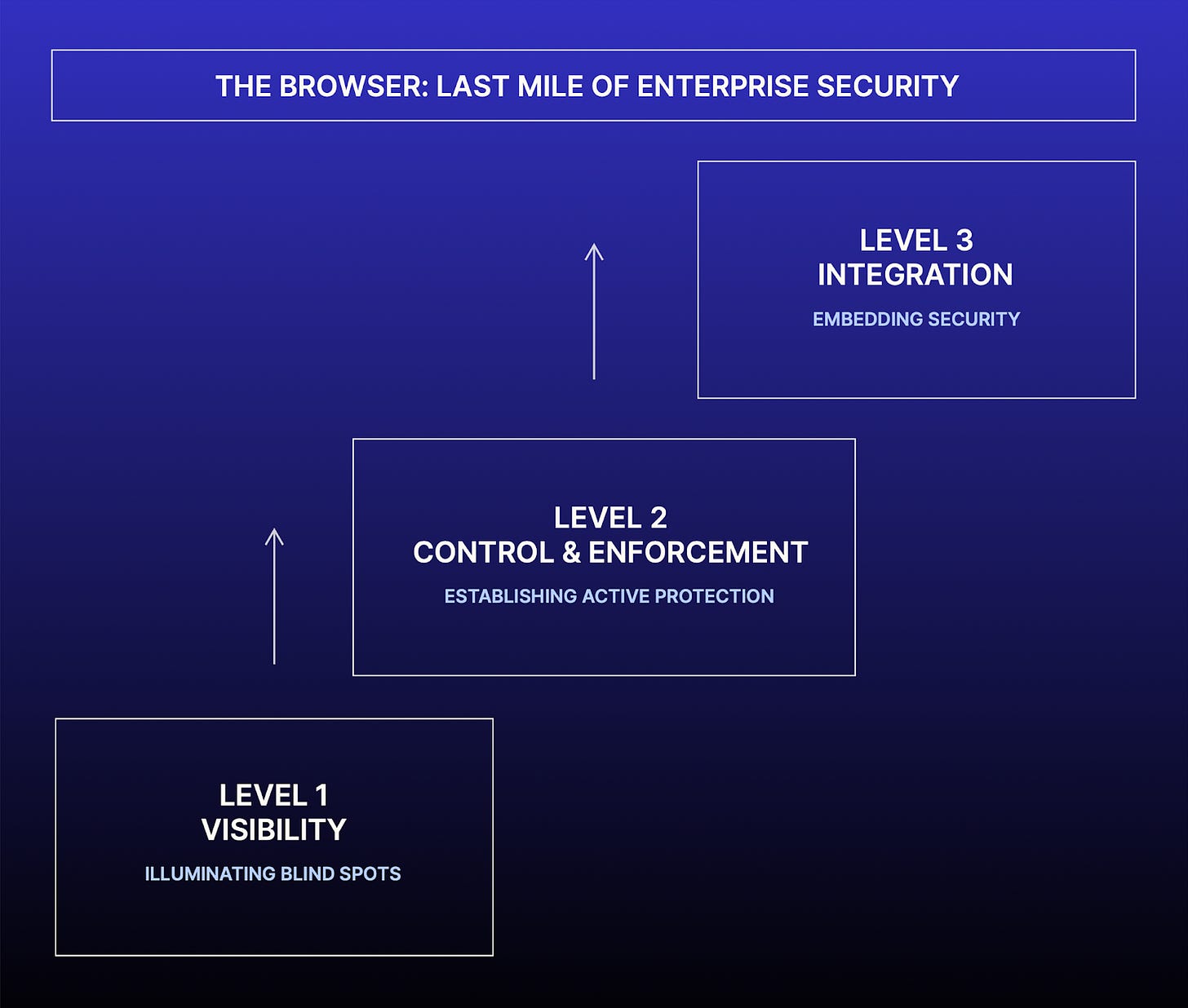
The Browser Security Maturity Model
To systematically close the browser security gap, enterprises should approach the problem in phases. We propose a Browser Security Maturity Model organized around three key pillars: Visibility, Control & Enforcement, and Integration & Usability. Each pillar builds upon the previous, guiding organizations from basic awareness to proactive control to a fully integrated and user-aligned security program. Below, we outline the stages of this maturity model and what capabilities and outcomes define each stage.
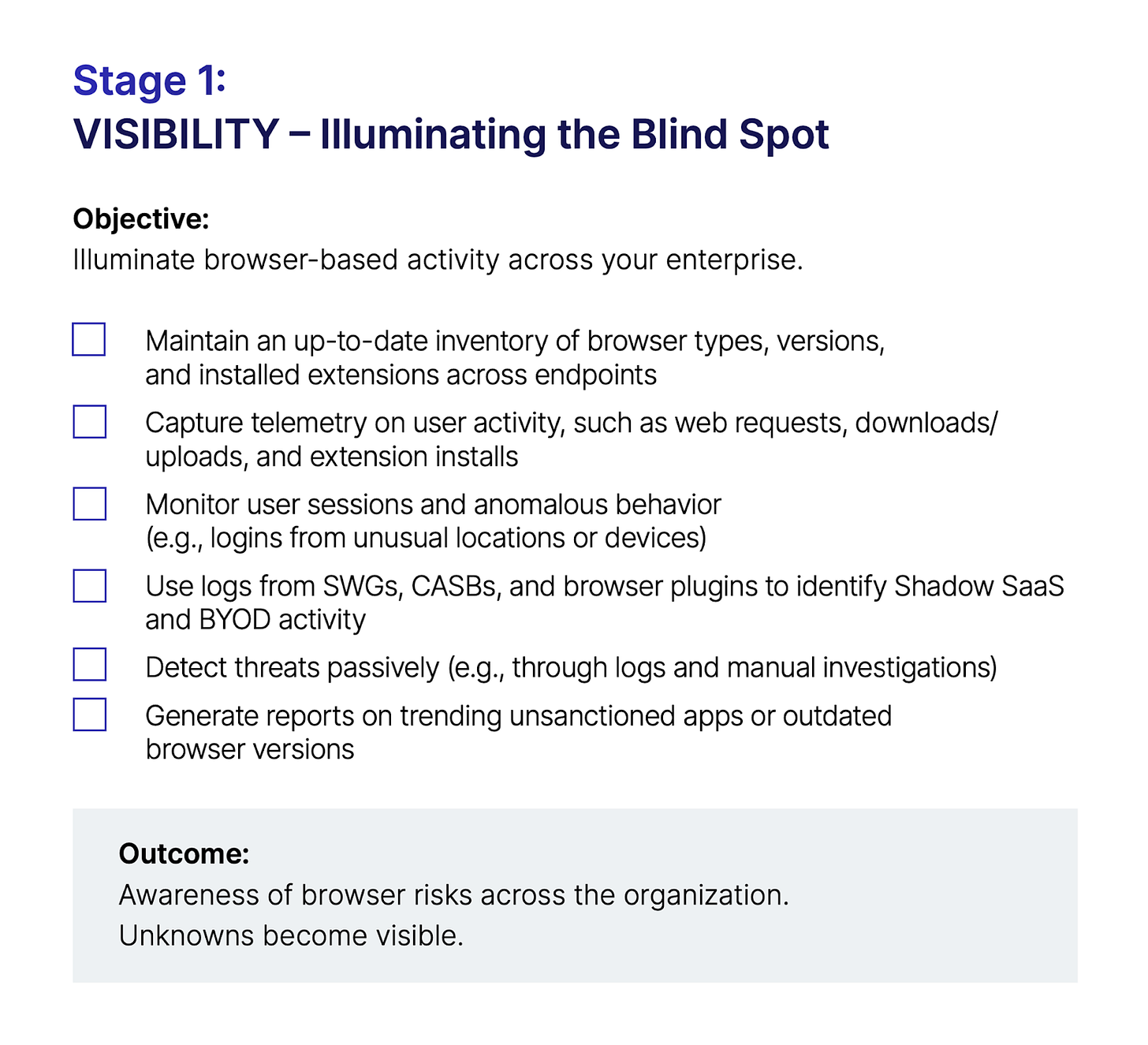
Stage 1
Visibility – Illuminating the Blind Spot
Objective: “You can’t protect what you can’t see.” The first stage focuses on gaining visibility into browser usage and risks across the enterprise. This is the foundational layer of maturity, giving security teams insight into who is doing what in which browser, on which device, and where corporate data is going in the web ecosystem.
Capabilities at this stage:
Inventory and Telemetry: The organization establishes an inventory of browsers in use (Chrome, Edge, Firefox, etc.), their versions, and the extensions installed on them. It also begins collecting telemetry on browser-based activity. This could involve enabling detailed logging on secure web gateways, using endpoint agents or browser plugins to capture web requests, or leveraging cloud proxy logs. The goal is to map out the “browser attack surface”, for e.g., how many unmanaged devices are accessing corporate apps? What SaaS services are employees using via their browsers? Which users have risky extensions?
User and Session Monitoring: At the visibility stage, security teams implement monitoring to capture critical events such as: file downloads and uploads via web, data copy-paste actions in web forms, new extension installations, and anomalous user behavior (like logging into corporate apps at odd hours or from new locations). For managed devices, this might come from EDR telemetry or a dedicated browser security extension reporting activities. For unmanaged devices, solutions like browser-based secure access portals or CASB browser plugins can provide some insight even if full control is not in place yet.
Threat Detection (Passive): With basic visibility, organizations can start detecting suspicious patterns. For example, if one browser process suddenly initiates an unusual outbound connection or if a normally office-based worker’s account is pulling large data from SharePoint via a browser late at night, these can be flagged for investigation. At Stage 1, detection might be mostly reactive (analysts reviewing logs or alerts after the fact) since enforcement isn’t fully in place yet. The key is that the security team is no longer blind but there is a trail to follow.
Example Outcome: A Stage 1 organization can, for instance, identify that a certain unsanctioned SaaS app is trending in use because the logs show multiple employees uploading data to it. They gain the insight to inform policy, even if they haven’t enforced one yet. Similarly, they might discover via telemetry that an outdated browser version is being used on many BYOD Macs, prompting an advisory to update (or a plan to enforce version control in the future).
Maturity characteristics: At the Visibility stage, an enterprise moves from having no idea what browser-based risks exist to having concrete data. This stage often involves cross-functional buy-in, getting IT to assist in deploying logging or lightweight extensions, and ensuring privacy considerations are managed (especially if monitoring user activity on personal devices). Success at Stage 1 is measured by the reduction of unknowns. When a security leader can confidently answer, “Which web apps are people using without approval? Which high-risk browser activities occurred this week?”; the organization has achieved the visibility milestone.
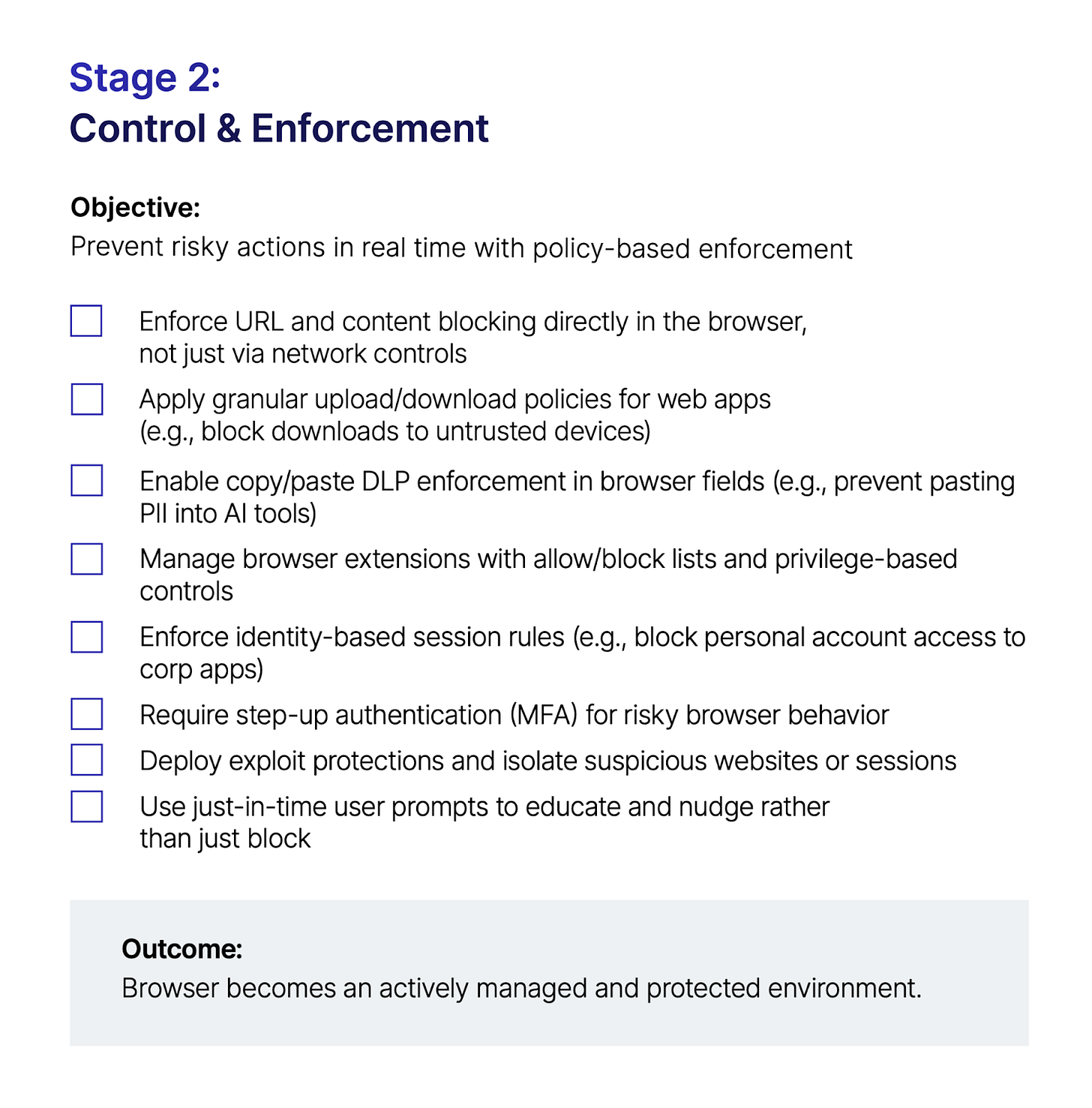
Stage 2
Control & Enforcement – Establishing Active Protection
Objective: Now that you have visibility, the next stage is to actively enforce security policies in the browser environment. Control & Enforcement means the organization doesn’t just observe risky behavior; it can prevent or contain it in real time. This is where the browser moves from being a passive window to an actively managed workspace.
Capabilities at this stage:
Policy-Based Controls: The enterprise deploys tools to implement granular browser policies. This can be done via an enterprise browser (a managed web browser provided by IT) or a browser security extension that works across standard browsers. Key policies include:
Malicious Content Blocking: Blocking access to known phishing sites, malware domains, or other dangerous URLs at the browser level (augmenting network SWG filtering). If a user somehow bypasses the VPN or is off the network, the policy still travels with the browser/extension to stop them from visiting known bad sites.
Download and Upload Controls: Enforcing rules like “Sensitive data from App X cannot be downloaded to an untrusted device” or “Users cannot upload files from this secure application to external sites.” For example, preventing a user from downloading a customer database from Salesforce onto a personal laptop, or blocking the upload of any file containing confidential keywords to a personal Gmail or Dropbox via the browser. Many CASB solutions offer API-based controls for major apps; at Stage 2, the organization extends this to any web interaction through the browser security layer.
Data Loss Prevention in Web Flows: Integrating DLP classifiers with the browser so that copying text or data out of certain web pages can be intercepted. For instance, if an employee attempts to paste a list of client Social Security Numbers into a ChatGPT prompt, the browser/extension can detect the sensitive pattern and stop the action or redact the data. This fine-grained DLP control was historically very difficult but at maturity Stage 2, the enterprise now has the means to enforce it in the browser in real time.
Extension Management: Actively controlling which browser extensions can be installed. This might mean maintaining an “allow list” of approved extensions and blocking all others, or at least flagging and removing known risky extensions (like those not published through official stores or those requesting overly broad permissions). An enterprise browser product might have this built-in, whereas an extension-based approach can report on installed add-ons and optionally disable or lock down certain ones. The organization may also enforce that only managed/provisioned browsers are used for work, to ensure these extension policies are effective.
Identity and Session Security: At this stage, organizations can enforce identity-centric policies in the browser. For example, preventing users from logging into corporate apps with personal accounts or vice versa (to avoid cross-contamination of personal and work sessions). The browser can enforce that only the corporate SSO is used to access certain services, eliminating “shadow identities” where an employee might create an account outside of single sign-on. Additionally, the browser can require step-up authentication (MFA) if a session becomes high-risk, say a user tries to access an HR system from an unusual location or attempts to download an unusually large amount of data. By tying into the organization’s identity platform, the browser security tool ensures session integrity and that trust is continuously validated.
Hardening and Exploit Protection: With an enterprise-controlled browser environment, additional hardening measures can be in place. This includes enforcing up-to-date browser versions (no more risky outdated plugins), running suspicious sites in an isolated mode (some enterprise browsers can automatically isolate or render untrusted sites read-only), and blocking exploits. While no solution can guarantee stopping a brand new browser exploit, having an enterprise browser or extension means if a known bad script or exploit kit is detected, it can be terminated immediately. Moreover, by reducing the attack surface (e.g., disabling potentially vulnerable legacy features like Flash, or disallowing silent installs of extensions), the likelihood of exploit success is lowered.
User Warnings and Education: Stage 2 isn’t just about outright blocking; it can include nudging the user when something looks risky. For instance, if an employee is about to upload a file containing sensitive data to an unsanctioned app, the browser might prompt: “This action violates company policy. Are you sure?”, giving them a chance to reconsider (or to justify a business need through an exception process). These just-in-time warnings can educate users and reduce accidental breaches without always resorting to a hard block.
Example Outcome: A concrete example at this stage: Suppose an employee receives a phishing link on their personal email and clicks it on a work browser. Instead of relying on them noticing the scam, the browser’s built-in protection immediately recognizes the fake login page and blocks it, showing a warning banner. In another scenario, an employee tries to copy data from a confidential report and paste it into a ChatGPT web session. The security extension detects the sensitive content and prevents the paste, logging an incident for IT. The attempted action is blocked in the moment, averting a potential data leak that Stage 1 visibility alone would only catch after the fact. The organization now actively intercepts risky behavior before damage occurs.
Maturity characteristics: Achieving Stage 2 means the enterprise has moved from observation to action. Policies are enforced uniformly regardless of device or network, which is crucial for filling the BYOD and remote work gap. At this point, security leadership can demonstrate measurable risk reduction, for e.g., “In the last quarter, 200 instances of data exposure were prevented by browser controls,” or “All high-risk unapproved extensions were removed from employee browsers.” There is also an increase in user trust and awareness, as employees see security prompts reminding them of safe practices. However, implementing controls must be done carefully; too heavy-handed and users will seek workarounds (which is why Stage 3 focuses on balancing security with usability). The key hallmark of Stage 2 is that the organization can mitigate browser-based threats in real time, significantly reducing the likelihood of a browser-led breach.
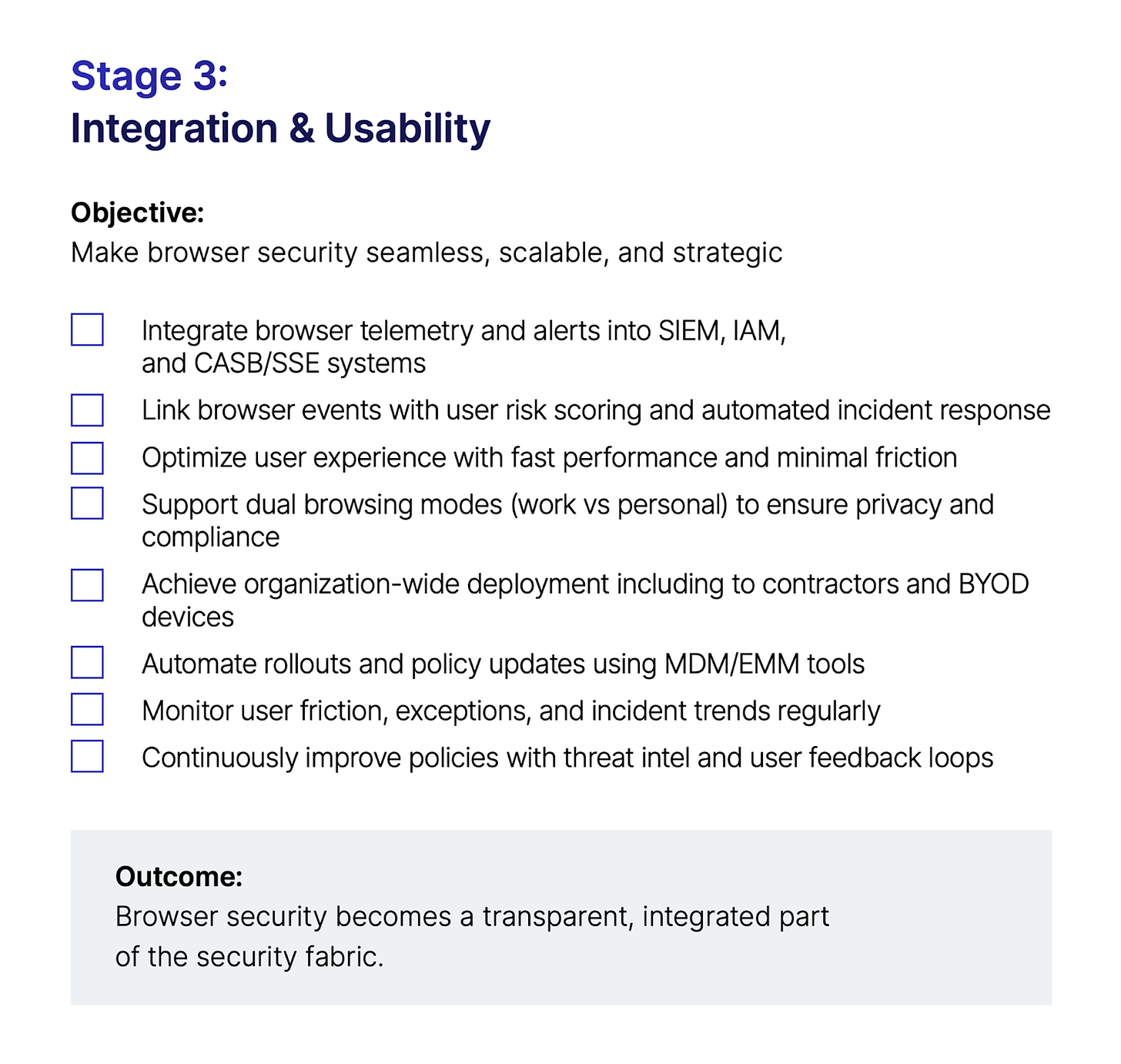
Stage 3
Integration & Usability – Security Woven into the Ecosystem
Objective: In the final maturity stage, browser security is fully integrated into the enterprise’s security ecosystem and optimized for minimal friction. This stage is about cementing the gains from Stages 1 and 2 by ensuring they work in harmony with other tools and that users embrace the secure browser environment rather than resist it. Integration & Usability focuses on embedding browser security into workflows and infrastructure so that it becomes an enabler for the business with little downside.
Capabilities at this stage:
Ecosystem Integration: All the data and controls from the browser are integrated with the broader security operations. Logs and alerts from the browser/extension feed into the Security Information and Event Management (SIEM) system, where they correlate with other alerts (like CASB or network events) to give a unified view. For example, if a user triggers a DLP alert in the browser and shortly after an EDR alert fires on their device, the SOC can see the connection in one place. Integration also means tying browser security into Identity and Access Management (IAM) and Zero Trust Network Access (ZTNA) policies. If a user’s risk level in the Identity Provider (say via a user behavior risk score) rises, that can signal the enterprise browser to adjust policies (like requiring MFA for all actions). Conversely, if the browser detects anomalous behavior, it could inform the identity platform to step up authentication or even suspend the session. Integration with CASB/SSE is also key, rather than operating in a silo, the browser security should share context with cloud security gateways (for instance, a cloud DLP event detected by CASB could trigger the enterprise browser to lock down that user’s download ability in real time). By Stage 3, the browser security solution is not an island; it’s a fully connected part of the security fabric.
Usability and User Experience: A hallmark of maturity is achieving security without sacrificing user productivity. At Stage 3, organizations fine-tune policies to eliminate unnecessary blocks or alerts. They leverage context-aware rules so that users are only challenged or stopped when truly needed (e.g., a user in the office on a managed device might have more leniency than an unrecognized device on a foreign network). Performance optimization is also addressed; the secure browser or extension must run efficiently. Enterprises might work with vendors to ensure that security overhead (like content scanning) doesn’t slow down critical web applications. Many secure enterprise browsers are built on Chromium, meaning users retain a familiar interface and compatibility with web apps, easing adoption. At this stage, companies also implement clear communication and training: users understand that the secure browser is there to protect them, not to spy on them. For instance, if the enterprise browser has a “work mode” and a “personal mode” (some solutions offer isolated profiles to separate corporate and personal browsing), employees are educated on how to use these modes so that their personal privacy is respected while work activity is protected.
Broad Deployment & Platform Coverage: By Stage 3, the secure browser solution (or the security extension) is deployed organization-wide, including to contract workers and third parties where appropriate. It supports all major operating systems and perhaps mobile browsers as well, giving a consistent safety net. Deployment at this scale requires automation and integration with device management solutions (MDM/EMM), to push the browser or extension and ensure it’s always running. The “rapid and streamlined deployment” aspect is key; mature programs have mastered how to roll out updates and new policies to thousands of endpoints with minimal disruption.
Continuous Improvement & Metrics: Finally, an integrated, mature program uses metrics and feedback loops. The security team tracks metrics like user friction (how often are users hitting false positives?), policy exceptions, and incident rates. They regularly review and update browser policies based on threat intelligence and user feedback. Integration with threat intelligence might automatically update blocklists or extension risk ratings. The program also keeps an eye on compliance requirements; by Stage 3, many organizations can confidently answer auditors on questions like “How do you control access to sensitive data via the web?” because they have a documented, active browser security program. The maturity at this stage means browser security is not a one-off project but an ongoing practice within the security organization’s governance.
Example Outcome: In a Stage 3 scenario, imagine a new zero-day vulnerability is announced for Chrome. A mature enterprise has multiple layers ready: their browser management platform immediately pushes a config to temporarily disable the vulnerable feature, their SOC gets intelligence feeds through the SIEM to watch for any exploit attempts in browser logs, and users get a notification via the secure browser about an emergency update with instructions. Meanwhile, because the enterprise browser runs in a hardened mode, even if someone encounters the exploit before patching, the damage is contained by additional sandboxing. On the usability front, employees have grown accustomed to the enterprise’s secure browser, for example, a consultant using a personal MacBook simply launches the company’s secure browser when accessing client data, and does everything else in their regular browser. They appreciate that the secure browser lets them work from anywhere without needing a clunky VPN or VDI, while the company is assured that all necessary controls (no downloads, copy/paste restrictions, etc.) are in effect for that session. Security has become a transparent facilitator rather than an obstacle.
Maturity characteristics: At the Integration & Usability stage, browser security is “baked in.” The organization experiences fewer incidents, and when incidents do occur, response is faster because the browser telemetry is integrated with incident response tools. Users, from entry-level employees to senior executives, have largely accepted the secure browser controls as a normal part of the workflow (much like they accepted badge access to buildings or multifactor login, it’s seen as a standard security practice). The CISO can report to the board that the company has a robust program safeguarding that last mile, with metrics to prove its effectiveness (e.g., reductions in data leakage events, compliance audit pass rates, improved mean time to detect/respond to browser threats). In essence, the enterprise has turned the browser from a liability into an asset; a controlled gateway that enhances security.
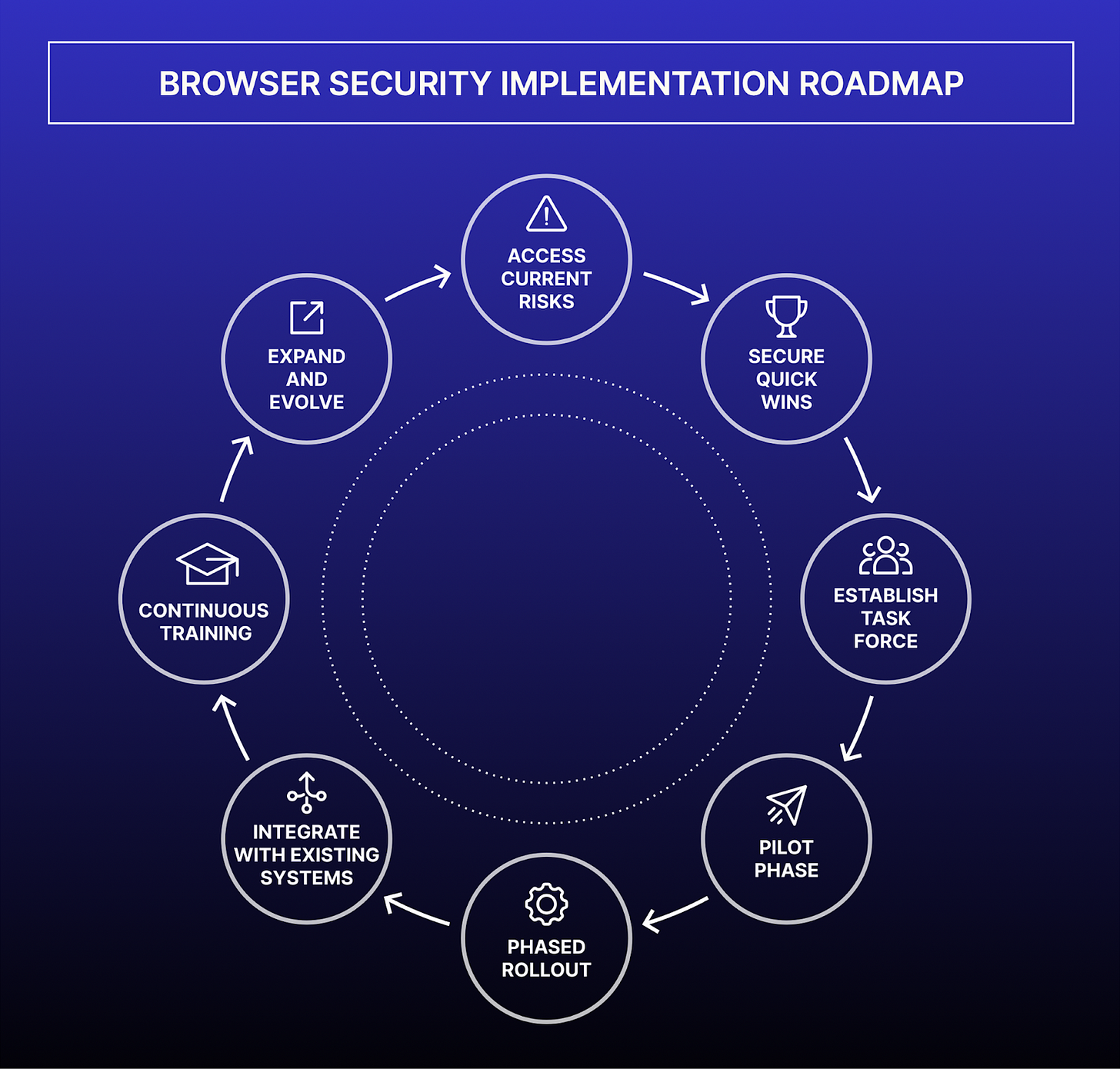
Implementation Roadmap: From Quick Wins to Full Browser Security
Adopting an enterprise browser security program is a journey. Below is a step-by-step roadmap and checklist to help security leaders progress through the maturity stages in a structured way. This roadmap is intended to be practical and modular, organizations can start with the basics and layer on more capabilities over time.
Assess the Current State and Risks – Begin with a frank assessment of your organization’s browser exposure. Inventory how corporate data is accessed via browsers today: What devices (managed/unmanaged) are used? Which critical SaaS apps are in play? How are you currently monitoring (if at all) browser activity? Identify recent incidents or near-misses involving browser use (e.g., phishing clicks, unsanctioned app usage, data leaks). This assessment should reveal the most pressing gaps, for example, maybe you discover that 30% of your workforce uses personal laptops for work with no browser protections in place, or that employees have installed dozens of unknown extensions. Use this to build urgency and executive buy-in. A useful exercise is to simulate a “day in the life” of a remote employee and see how many security policies they can bypass via a web browser – the findings often make the case for action.
Secure Quick Wins in Visibility – Tackle the low-hanging fruit to get immediate visibility. For instance, enable logging on existing infrastructure: ensure your SWG or firewall is logging all web requests with user IDs. If you have an MDM for corporate devices, use it to collect a list of installed browser extensions or enforce that browsers report basic telemetry. Deploy a lightweight CASB discovery tool or even analyze proxy logs to find top unsanctioned apps in use. If possible, deploy a browser security extension in audit mode to a pilot group; this can start feeding you data on user actions (without blocking anything yet). Quick wins might also include updating policies, such as mandating that all employees use the corporate SSO in their browser for accessing company apps (to centralize identity tracking) and require any BYOD device to register with an identity provider or gateway before accessing key apps (so at least you know the device/browser that’s coming in). These steps begin illuminating the blind spots with minimal disruption.
Establish a Cross-Functional Task Force – In parallel, form a small team or task force that includes security architects, IT endpoint management, identity specialists, and representatives from compliance and helpdesk. Browser security touches many domains (endpoint, network, cloud, user experience), so you need alignment. This team will evaluate solutions (enterprise browsers vs. extensions or both), design policies, and coordinate deployment. Getting early input from the IT support teams is key; they will field user questions and ensure that new tools don’t conflict with existing device configurations. Also loop in a few tech-savvy end-users or champions from different departments to pilot and give feedback.
Pilot Phase (Visibility to Control) – Choose a segment of the organization to pilot the new browser security approach. This could be one department or a group of power users who deal with sensitive data (e.g., finance or R&D team). During the pilot, deploy the chosen solution (for example, roll out an enterprise secure browser or a security extension) to their devices. Start in a monitoring-only mode for a short period: collect visibility on their browser usage patterns and confirm the solution is stable in their environment. Then gradually enable a few core control policies for this pilot group. Good starting policies are ones with clear benefit and low controversy, e.g.: block known malicious sites, enforce login via SSO for corp apps, and maybe block a handful of obviously dangerous extensions. Provide the pilot users with training on what to expect (e.g., “you might see a block page if you hit a malicious site, here’s how to report false alarms”). Closely monitor the pilot, gather feedback, and adjust as needed. Success in the pilot will pave the way for broader roll-out, capture metrics like “We blocked X threats and detected Y unsafe behaviors in the first month” to help build the case.
Roll Out Full Controls in Phases – With lessons learned from the pilot, begin broad deployment across the enterprise. A phased rollout can mitigate risk: for example, enable the secure browser/extension for all users in a region or business unit first, then others. Alternatively, roll out with a subset of policies (maybe start with all visibility + blocking the worst threats) and later turn on stricter data protection rules. Communicate clearly to users about what is changing and why: emphasize that the secure browsing environment protects them and the company, and provide examples of prevented incidents (without blame). Ensure there’s an easy process for users to request help or policy exceptions if something critical is blocked, this will keep trust high. During rollout, it’s crucial to avoid major disruption: track any increase in IT support tickets, and if a particular policy generates too many false positives, dial it back and refine it rather than let it erode confidence in the whole initiative.
Integrate with Existing Systems – As the browser security solution becomes enterprise-wide, focus on integration. Hook the browser logs and alerts into your SIEM or XDR platform so analysts have a single pane of glass. Integrate with your incident response playbooks, for e.g., if a serious malware threat is detected via the browser, have automated actions like isolating that endpoint or expiring all active sessions for that user. Work with your identity team to feed browser risk signals (like an anomalous login via browser) into user risk scores. Align the browser controls with DLP classification: if you have data labeled as “Confidential”, make sure the browser policy knows to treat that data differently (some enterprise browsers can read file classification tags or watermarking). The aim is that the new controls don’t operate in a silo but rather enhance what you already have. For instance, if you use Microsoft 365 DLP, ensure the browser doesn’t block the same thing in a conflicting way, instead, maybe the browser can enforce the M365 DLP policies on unmanaged devices. Integration will also involve working with compliance teams to map how the browser controls help meet regulatory requirements (document these mappings for audits).
Emphasize Usability and Continuous Training – After the initial rollout dust settles, shift focus to the user experience. Survey users or collect feedback on the secure browser: Are there websites that break or slow down? Are the prompts understandable? Use this input to fine-tune. Perhaps you discover that a certain developer tool website was falsely flagged; you can whitelist it. Or employees might be confused when switching between personal and work browsing contexts, provide clearer guidance or even technical separation (some solutions allow a “dual browsing” approach). Continue to run phishing drills or data handling training, but now incorporate the browser security usage into those (e.g., teach users how to recognize a block page and what to do). Make security a positive part of company culture: celebrate successes like “This quarter, our secure browsing protected us from 50 phishing attempts, great job staying vigilant and reporting issues!” When users see the value and feel part of the solution, they are more likely to cooperate than find workarounds.
Expand and Evolve – Finally, treat the browser security program as an evolving project. As new web-based technologies arise (say, a new AI collaboration tool), loop them into your security review. Continuously update your list of approved extensions and web apps. Evaluate enhancements like integrating remote browser isolation for the very high-risk clicks (some orgs choose to route unknown URLs through an isolation service while keeping the enterprise browser for normal work). Stay updated on the threat landscape: for example, if there’s a surge in token theft malware via browsers, consider adding additional credential protection measures (many enterprise browsers can secure stored passwords or detect token exfiltration attempts). Also, keep an eye on metrics: if you’ve achieved near-zero incidents in one category, maybe you can tighten another area now. As maturity grows, consider sharing your insights, for instance, contribute anonymized data about emerging browser threats to an information-sharing group in your industry. This not only helps the community but can also reinforce your program’s credibility to internal stakeholders.
By following this roadmap, organizations can move from acknowledging the browser as an uncontrolled risk to confidently managing it as a secure, integrated part of their environment. Each step should be tailored to the organization’s context, a highly regulated bank might move faster to enforce strict controls, whereas a tech company might emphasize user experience and gradual improvement. The key is forward momentum: every improvement in browser visibility or control directly reduces the likelihood of a costly breach or compliance failure in that “last mile.”
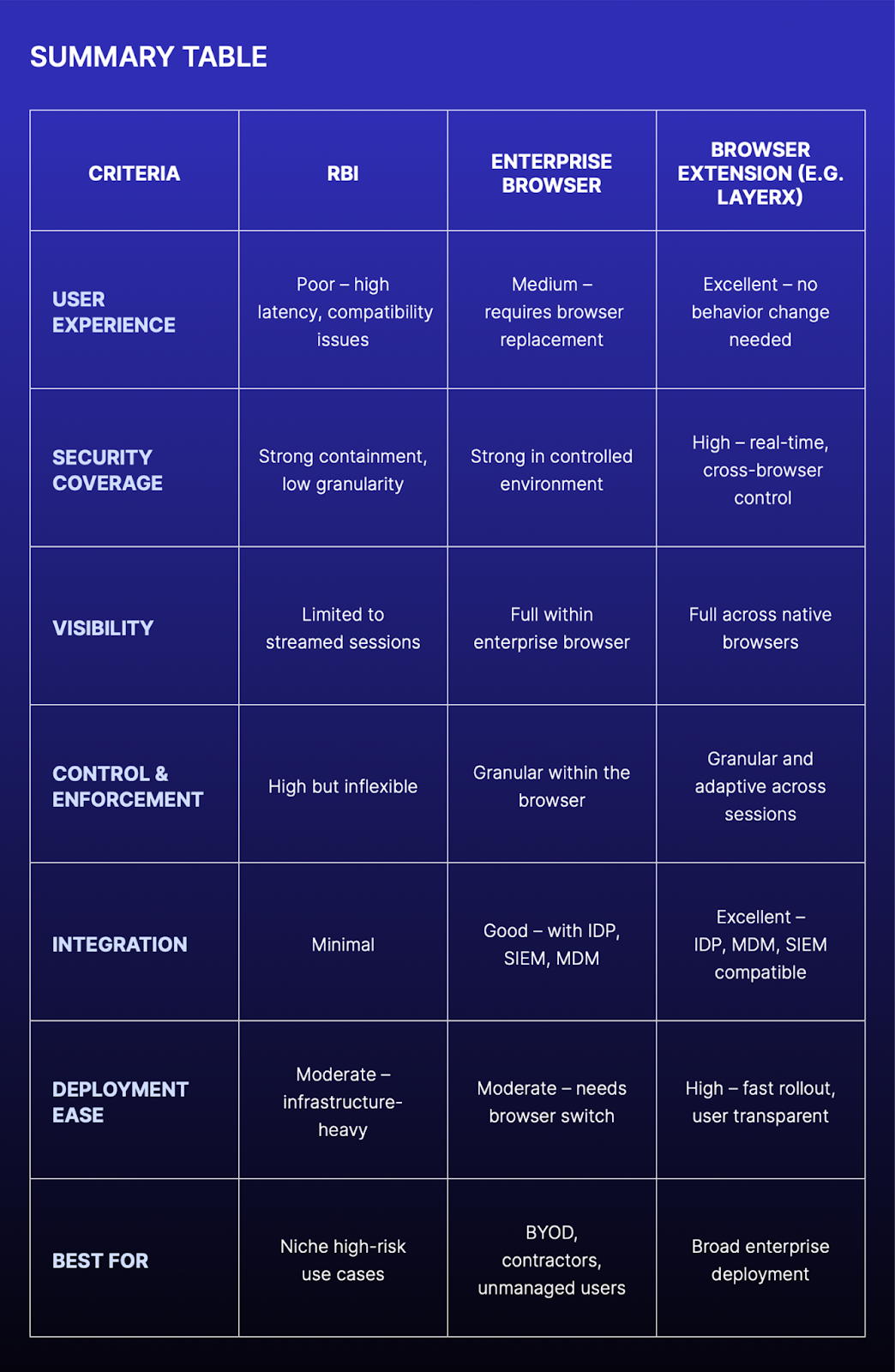
Comparing Browser Security Approaches: RBI vs Enterprise Browsers vs Extensions
As organizations evaluate how best to secure browser activity, three primary architectural models have emerged: Remote Browser Isolation (RBI), Enterprise Browsers, and Enterprise Browser Extensions. Each offers a different balance of security control and usability. This section compares them across the dimensions covered in this guide — Visibility, Control & Enforcement, and Integration & Usability — while highlighting key strengths and trade-offs.
Remote Browser Isolation (RBI)
RBI solutions work by streaming a remote, sandboxed browser session to the user, effectively isolating all web content from the endpoint. While this model offers strong containment — especially for unknown or high-risk websites — it suffers from significant drawbacks:
User Experience & Latency: Because all browsing is rendered in a remote server and streamed as a visual feed, RBI often introduces latency, degraded responsiveness, and visual artifacts. Rich web apps, video conferencing tools, and dynamic JavaScript-heavy websites tend to break or behave unpredictably.
Site Compatibility: Modern SaaS tools (e.g. Google Workspace, Figma, Salesforce) may not function properly when routed through RBI, especially when requiring real-time collaboration or third-party plug-ins.
User Resistance: RBI replaces the native browsing experience with a degraded alternative. Users frequently bypass RBI when given the option, undermining its efficacy.
Obsolescence: Most enterprises are phasing out RBI due to these usability issues. It is increasingly seen as an outdated control, useful only in rare, high-risk scenarios such as opening uncategorized links or isolating unknown downloads.
Enterprise Browsers (e.g. Island)
Enterprise Browsers are Chromium-based browsers that provide robust, policy-enforced security within a dedicated browser environment. While they offer strong controls, they also introduce friction:
Security Capabilities: These solutions offer deep visibility into browser activity, granular policy enforcement, and integration with enterprise systems (IDP, CASB, MDM, SIEM). They allow detailed control over downloads, copy/paste, SaaS access, and extension usage.
User Disruption: Enterprise Browsers require employees to switch away from their existing browsers (e.g. Chrome, Edge, Safari). This disrupts established workflows, browser profiles, bookmarks, and plugins. Adoption often stalls due to user resistance.
Limited Coverage: While they secure activity within the enterprise browser, any user activity outside that browser — including on personal or unmanaged browsers — is invisible to the system. For instance, a user copying sensitive data into ChatGPT from Chrome remains unmonitored if the enterprise browser wasn’t used.
Best Fit: Enterprise Browsers are often best suited for securing third-party contractors, unmanaged endpoints, or specific BYOD scenarios where control of the browser environment is necessary and user experience is less of a concern.
Enterprise Browser Extensions (e.g. LayerX)
Browser security extensions offer a lightweight, user-transparent way to layer security into existing browsers.
User Experience & Adoption: Extensions do not require users to change their preferred browser. Users retain their bookmarks, history, settings, and browser familiarity — eliminating friction. This dramatically improves adoption and compliance.
Visibility & Control: Modern browser extensions can provide rich telemetry on user activity (e.g. copy/paste, uploads, logins), enforce real-time DLP policies, detect shadow SaaS usage, and manage risky browser extensions — all without replacing the browser.
Deployment Flexibility: Enterprise-grade extensions can be deployed and enforced across all major browsers (Chrome, Edge, Firefox), including private/incognito modes. They can also integrate with enterprise systems like IDP, MDM, CASB, and SIEM.
Security Without Tradeoffs: Extensions provide an optimal balance between visibility, control, and usability — particularly in environments where security teams need to operate across both managed and unmanaged devices, without compromising user experience.
Concluding Sections:
As enterprises seek to secure their browser activity at scale, they are actively rethinking the role of the browser. Remote Browser Isolation (RBI) showed that containment can protect users, but at the expense of usability. The future belongs to Enterprise Browsers and Browser Extensions, which better reflect how people actually work. Increasingly, these should cover agentic browser solutions in our opinion.
Enterprise Browsers provide strong, policy-driven control and are best for contractors, BYOD, and unmanaged endpoints where a secure perimeter is critical. Browser Extensions offer protection inside the browsers employees already use, preserving usability while giving security teams visibility and control. This balance makes them ideal for knowledge workers on managed devices.
The browser is no longer just a window to the web, but it is becoming the operating layer of the AI economy. Security must evolve accordingly. The next generation of enterprise browsers and extensions will act as agentic security controls: validating intent, isolating memory, and applying Zero Trust principles not only to people but also to the AI agents acting on their behalf. Organizations that embrace this shift will transform the browser from the weakest link into a trusted foundation for the agentic era.
****
You can download the complete PDF guide here:



The container bit is what's moved fastest here. agent-browser recently shipped a pure Rust daemon that replaces the entire Node.js stack with a 6MB binary. Fewer dependencies to audit, smaller attack surface, way simpler container images. For the kind of enterprise deployments you're describing, it's a meaningful change. Dug into the technical side of it here: https://reading.sh/your-ai-agent-doesnt-need-node-js-to-browse-the-web-4f4e1f539d3a?sk=97adeb96d716818047ace4cd5c79d879